I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.
TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.
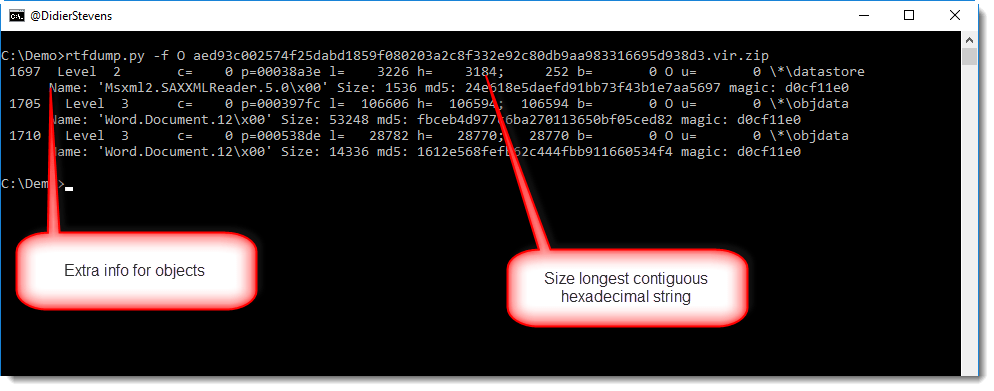
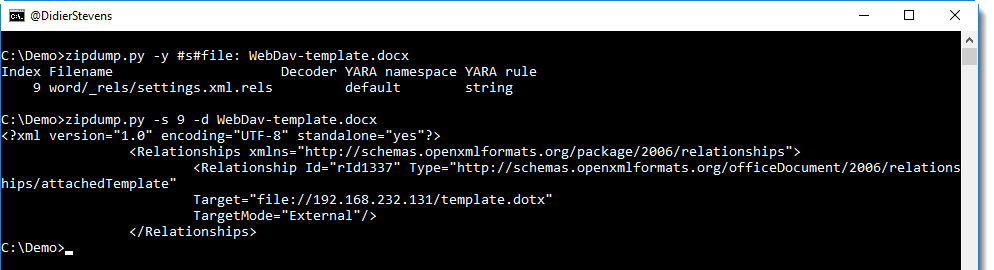
I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the other Windows 7 machine with Word 2016 and a .docx document with a remote template (template.dotx) (using the file:// URI scheme). The Windows firewall on the IIS machine was configured to block ports 139 and 445.
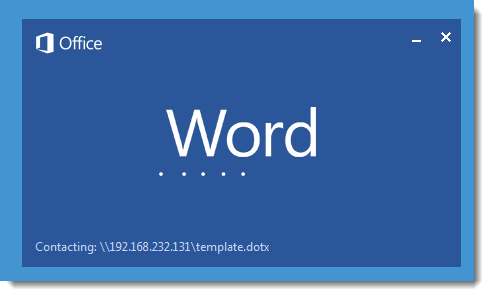
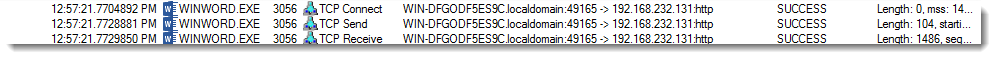
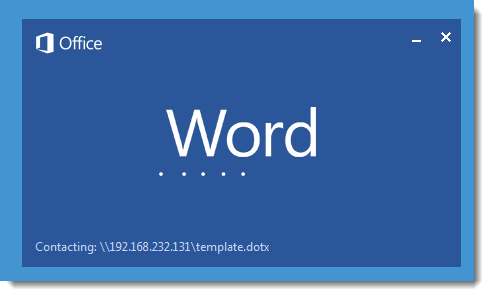
When the .docx document is opened, Word will retrieve the template:
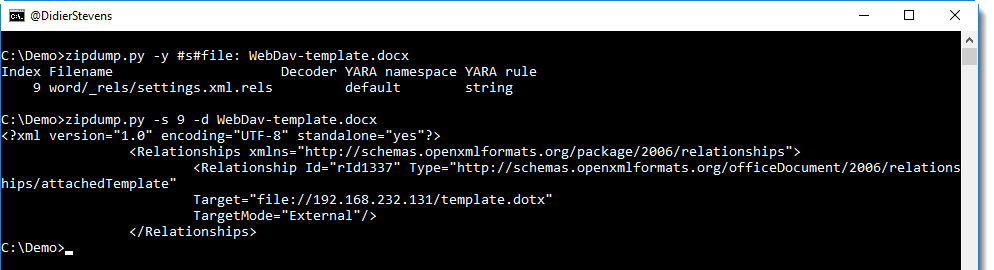
Here is the URI:
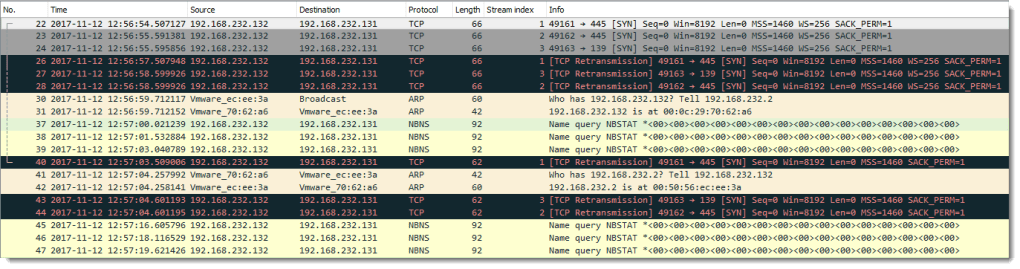
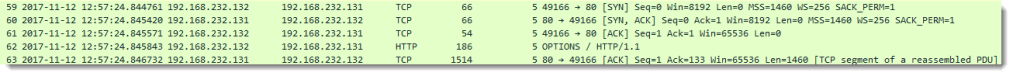
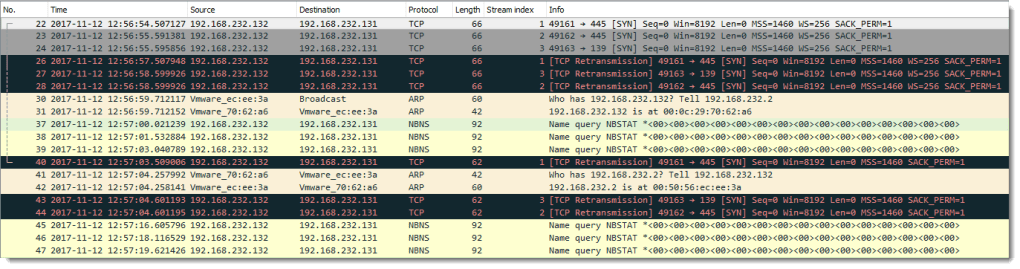
First we see attempts to connect on ports 445 and 139 on the IIS machine (SYN packets):
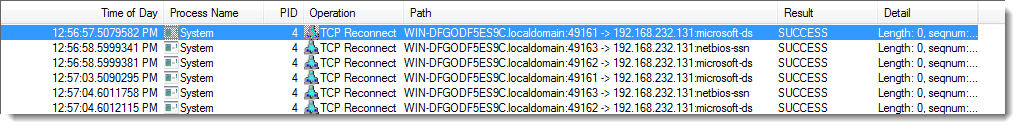
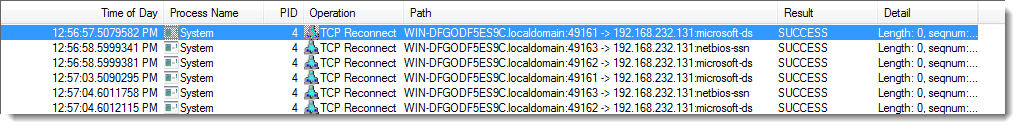
These come from the “System process”:
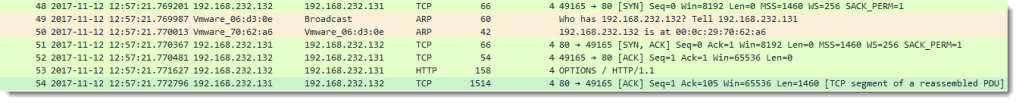
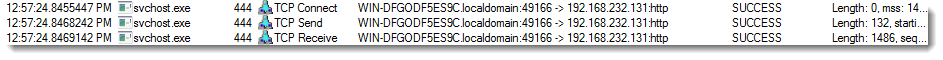
There are no packets coming back from the IIS machine (I blocked port 139 and 445), and after almost 30 seconds we see an HTTP request to port 80 on the IIS machine:
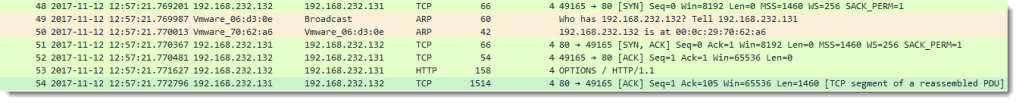
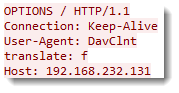
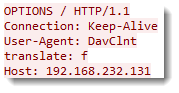
This is a WebDAV request, notice the User Agent string “DavClnt”:
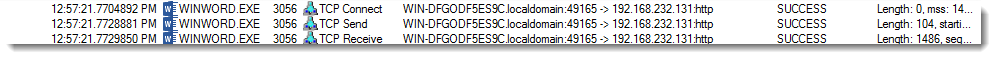
This TCP connection originates from the Word process:
And about 3 seconds after this request, we get another WebDAV request:
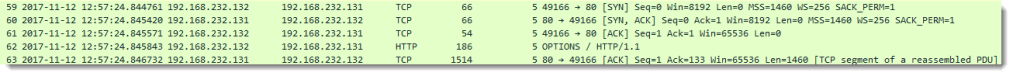
For this request, the User Agent string is “Microsoft-WebDAV-MiniRedir/6.1.7601”.
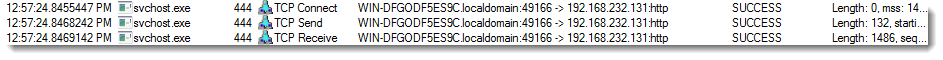
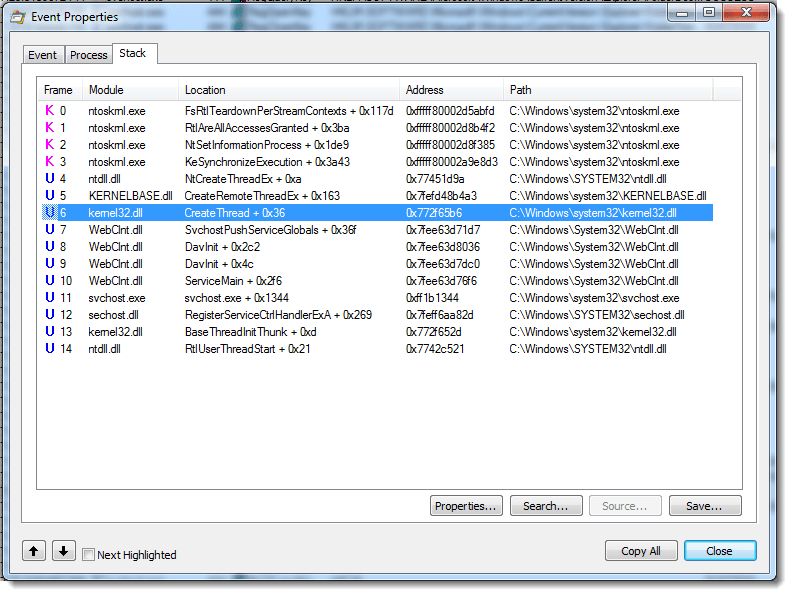
This TCP connection originates from the WebClient service:
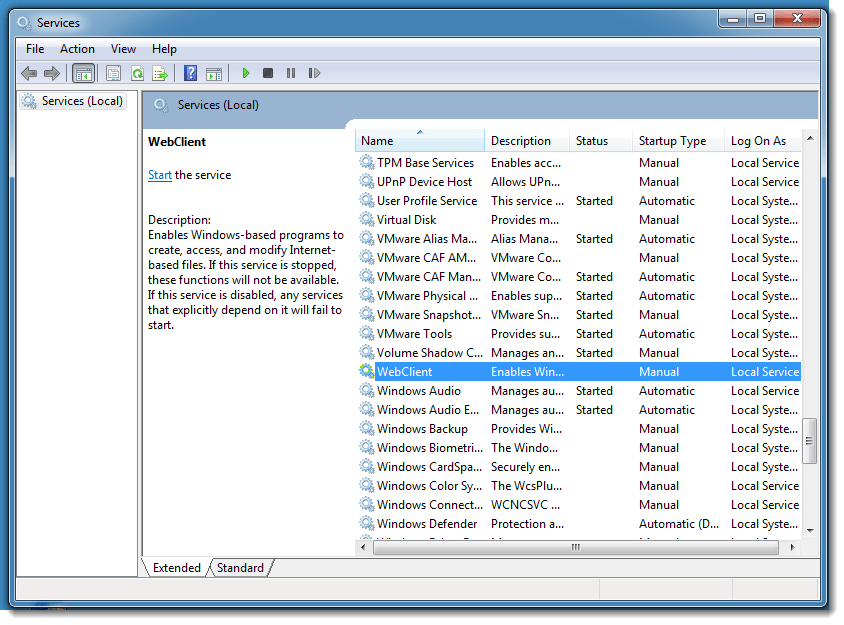
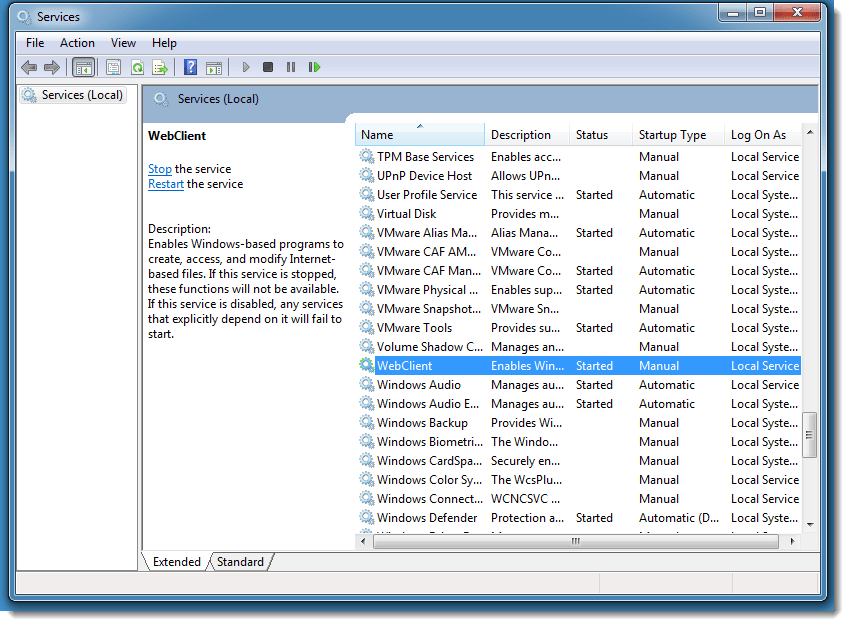
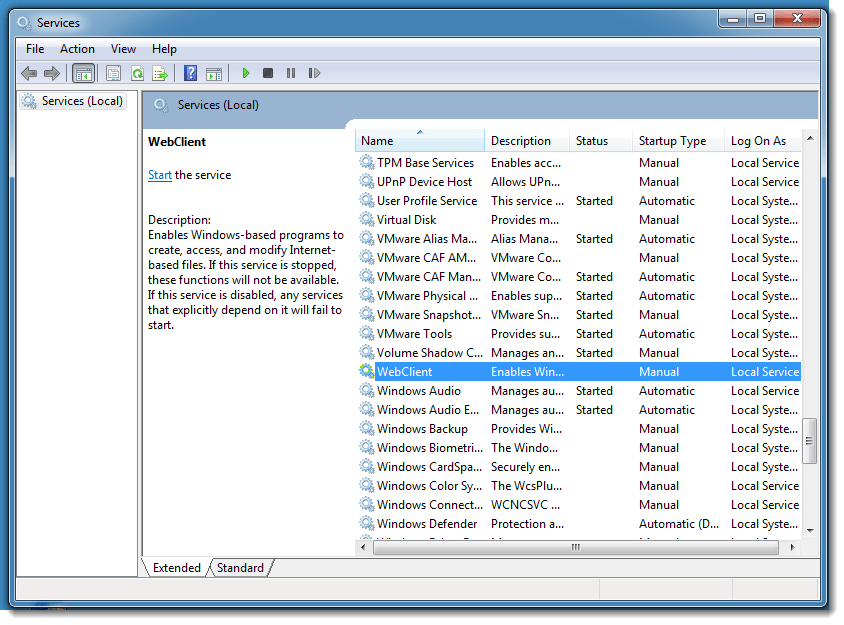
This service was not started:
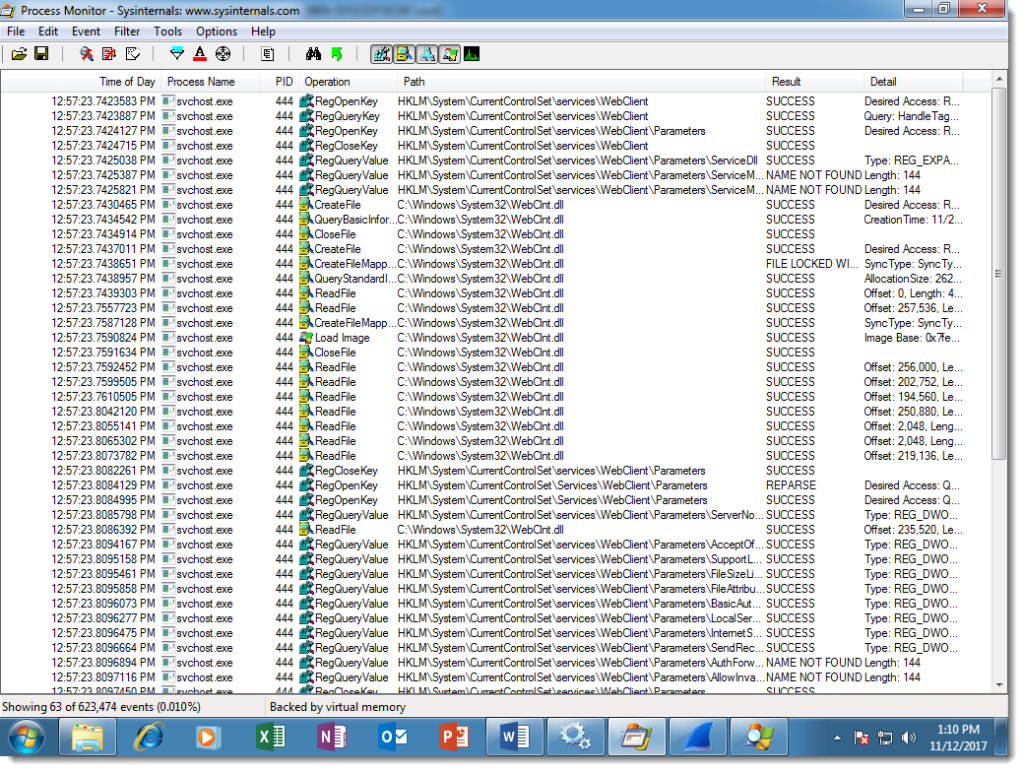
The svchost service host process will load and start the WebClient service:
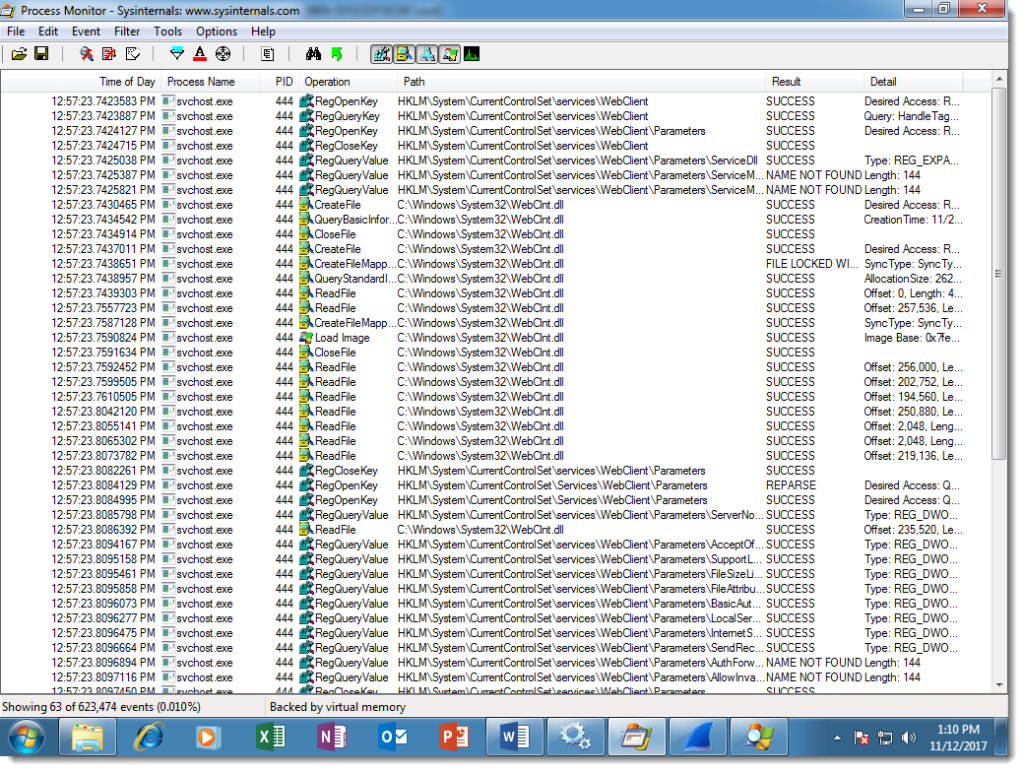
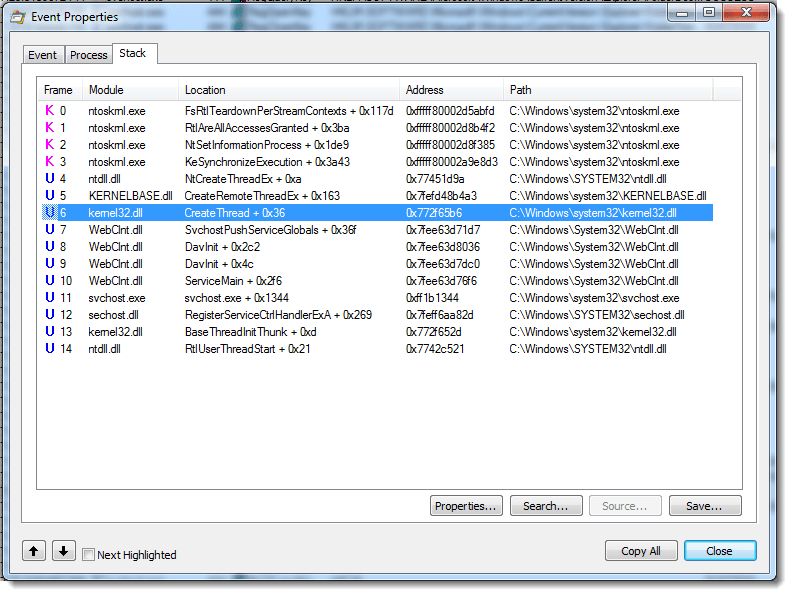
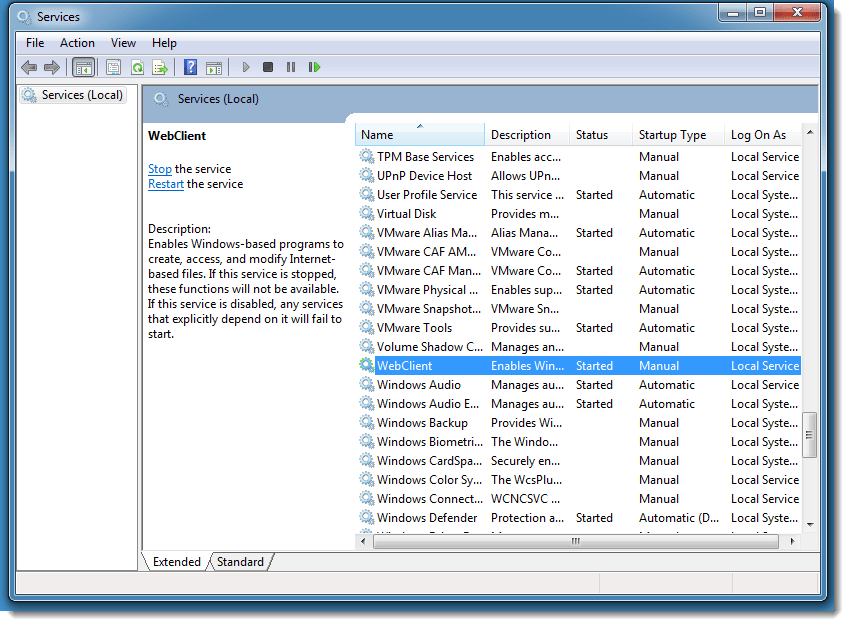
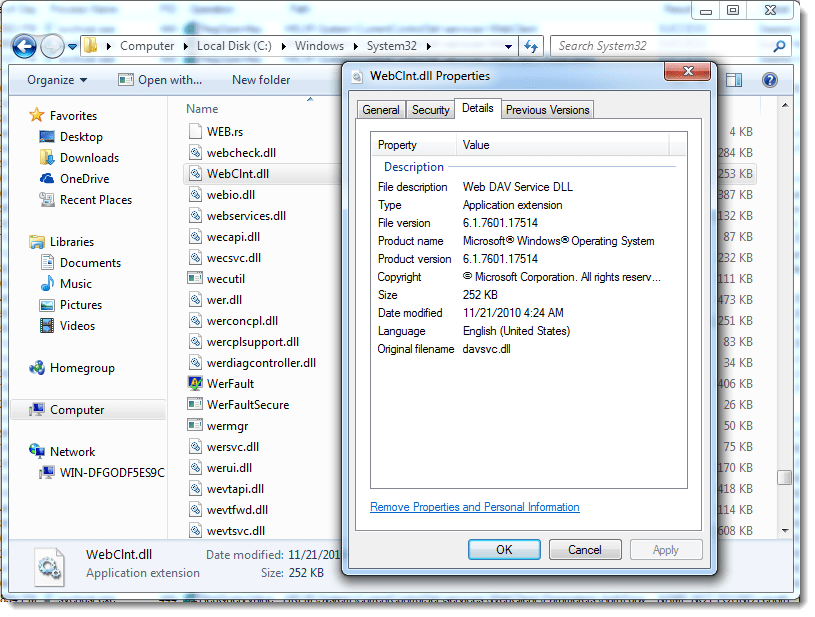
WebClient (WebClnt.dll) is the WebDAV service:
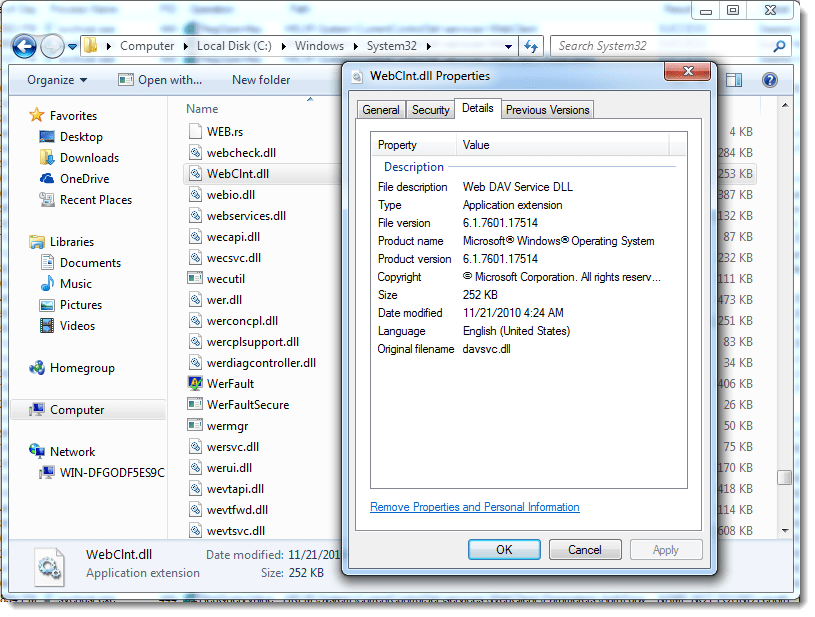
To summarize, when the file:// URI scheme is used in a Word document and SMB connections can not be established, we will see WebDAV requests from:
- Word (DavClnt)
- WebClient service (Microsoft-WebDAV-MiniRedir/6.1.7601)
I’ve observed the same behavior with Windows 10 (with a different version number for the WebClient User Agent string).
When the document is opened a second time, there is no WebDAV request from Word (1), only requests from the WebClient service (2).
When I stop the WebClient service and reopen the document, there is first a WebDAV request from Word (1) followed by requests from the WebClient service (2).
When I disable the WebClient service and reopen the document, there are no more WebDAV requests at all.