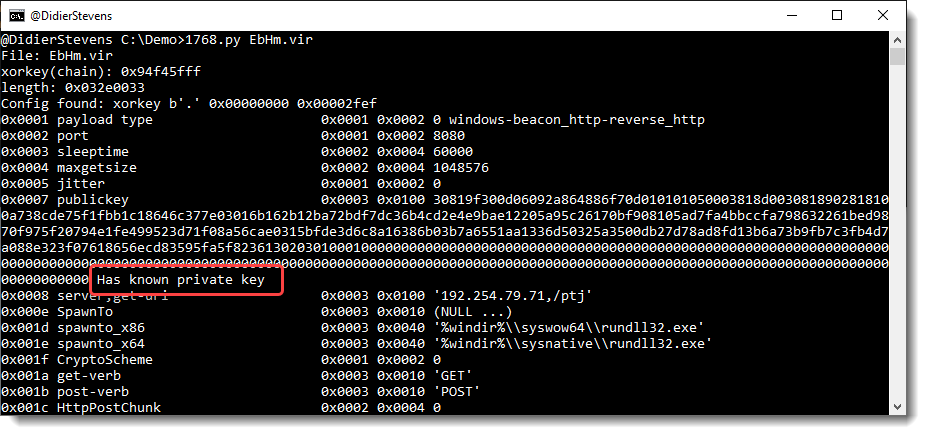
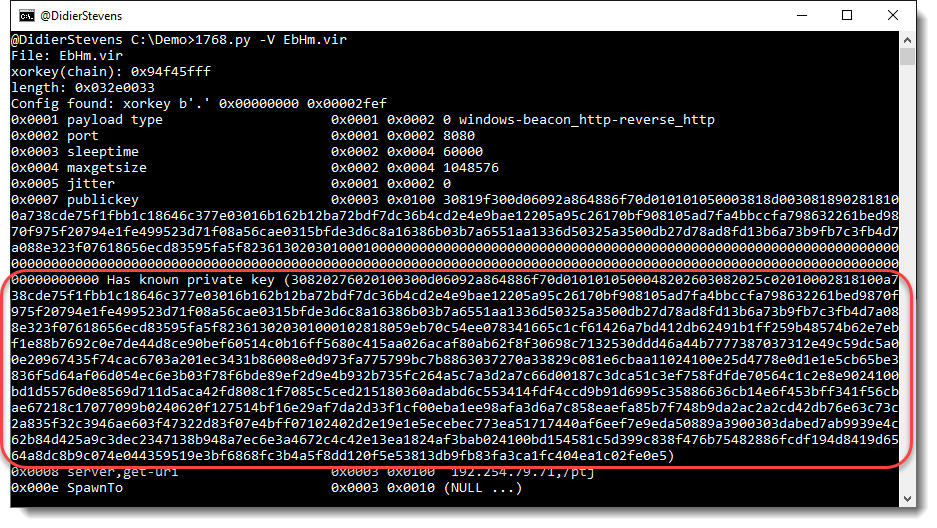
cs-decrypt-metadata.py is a new tool, developed to decrypt the metadata of a Cobalt Strike beacon.
An active beacon regularly checks in with its team server, transmitting medata (like the AES key, the username & machine name, …) that is encrypted with the team server’s private key.
This tool can decrypt this data, provided:
- you give it the file containing the private (and public) key, .cobaltstrike.beacon_keys (option -f)
- you give it the private key in hexadecimal format (option -p)
- the private key is one of the 6 keys in its repository (default behavior)
I will publish blog posts explaining how to use this tool.
Here is a quick example:

MD5: 31F94659163A6E044A011B0D82623413
SHA256: 50ED1820DC63009B579D7D894D4DD3C5F181CFC000CA83B2134100EE92EEDD9F