I’ve worked on a couple of new tools to analyze the digital signature found in PE files. In this post, I’m sharing some invalid signatures I found on my machines.
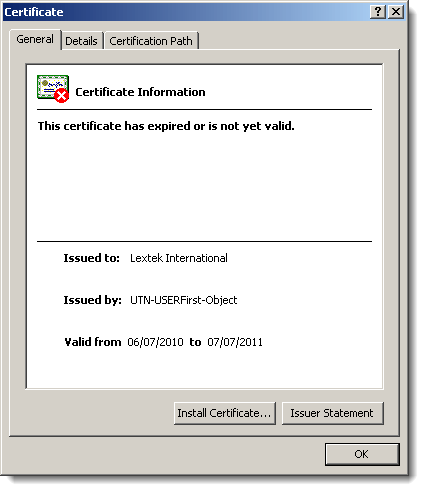
This signature is invalid because the certificate expired:
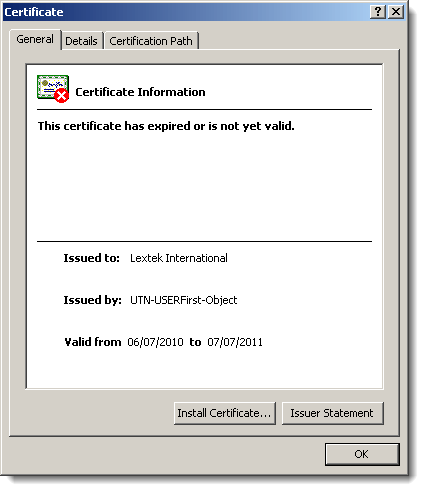
Normally, the fact that it expired shouldn’t cause the signature to become invalid, but here it does because the author forgot to countersign the signature with a timestamping service:

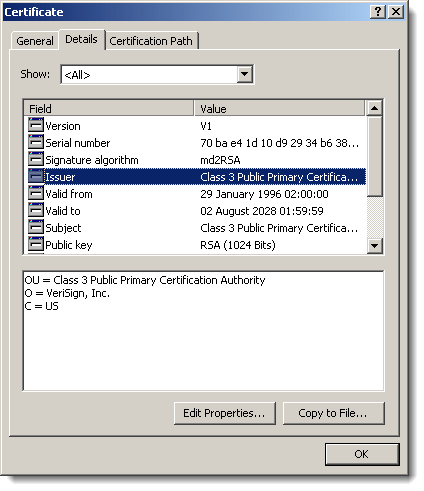
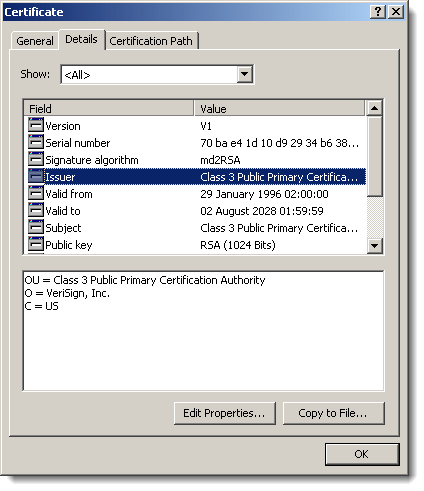
I also found several files where the root certificate used in the signatures uses a signature algorithm based on the MD2 hash:
And last a signature with a revoked certificate:

Remember Realtek Semiconductor? Their private key was compromised and used to sign Stuxnet components.