The ISSA Journal featured my article on Network Device Forensics, making it available to everyone.
And I’m giving a 2-day training on PDF at Hack In The Box Amsterdam 2013.
The ISSA Journal featured my article on Network Device Forensics, making it available to everyone.
And I’m giving a 2-day training on PDF at Hack In The Box Amsterdam 2013.
Today I received my 3th MVP award from Microsoft: MVP 2013 Consumer Security.

To celebrate this, I’ve 2 things for you:
datapipe_V0_0_0_1.zip (https)
MD5: 5BF1594E8144B694431E7A7E3BDF33F7
SHA256: 57CD06EBFEC1C5C2661E44260A7304DFCDEEB2F54132E0627A474AF756AFA956
I’ve added a new page to document my Authenticode Tools like AnalyzePESig.
It has a small explanation for each field found in the output of AnalyzePESig. For example, the fields Issuer Unique ID and Subject Unique ID should always be 0. In the case of the Flame certificate, they are not, because the Issuer Unique ID field was used to help produce the MD5 collision:
Filename: WuSetupV.exe.vir MD5: 1f61d280067e2564999cac20e386041c Entropy: 6.79663 ... Issuer unique ID chain: 887 Issuer unique ID chain: 0 Issuer unique ID chain: 0 Issuer unique ID chain: 0 Issuer unique ID chain: 0
I also use this tool to periodically review new executables on my machines.
My Windows x64 The Essentials Workshop at BruCON 2012 was a success. Today I finished the production of the videos of this workshop, it is for sale on my company’s site.
And tomorrow I’m doing my White Hat Shellcode Workshop at Hack.lu 2012, so I started a promotional sale during Hack.lu 2012.
I will release free stuff on my company’s website Didier Stevens Labs. Like this new XORSearch video.
XORSearch is one of my popular tools, but I hadn’t made a video for it yet:
I founded my own company: Didier Stevens Labs

You can find videos of my workshops for sale on this new website.
And I will give a brand new workshop at Brucon next week: Windows x64: The Essentials
I will sell CDs with my workshops videos at Brucon with a 20% discount.
I’ve worked on a couple of new tools to analyze the digital signature found in PE files. In this post, I’m sharing some invalid signatures I found on my machines.
This signature is invalid because the certificate expired:
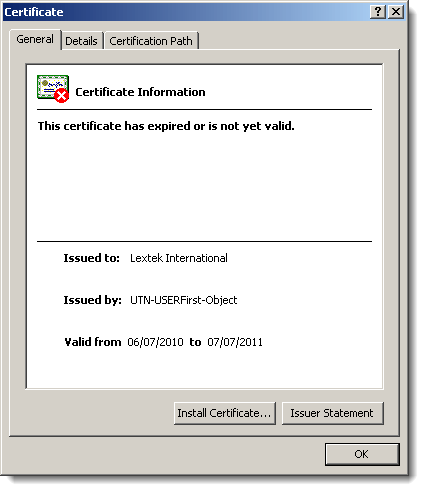
Normally, the fact that it expired shouldn’t cause the signature to become invalid, but here it does because the author forgot to countersign the signature with a timestamping service:

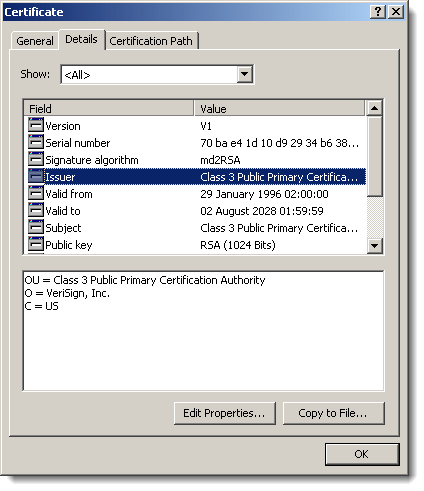
I also found several files where the root certificate used in the signatures uses a signature algorithm based on the MD2 hash:
And last a signature with a revoked certificate:

Remember Realtek Semiconductor? Their private key was compromised and used to sign Stuxnet components.
The latest (IN)SECURE Magazine issue includes my article on White Hat Shellcode.
Do you need to analyze a Cisco IOS Core Dump?
Read this.
“But that doesn’t explain how to analyze a core dump“, you say? Correct, unfortunately. That’s all you get with SOPA/PIPA enacted.
“But SOPA blackout day” was yesterday, you say? Correct. But I’m not following the crowd 😉