As I promised last week, here are the technical details of the Pocket EICAR Test File Server.
I bought a mini AVR web server from Tuxgraphics, it’s an AVR microcontroller with an Ethernet controller on a small PCB. The goal is to integrate some sensors (like temperature) and actuators (central heating) into my home network, but my first project was to learn to program it and develop a small web server framework.
The board is ready for operation, I just had to solder 2 wires to provide power and a programming connector. You’ll need an AVR In-System Programmer to upload your compiled C program to the microcontroller. Tuxgraphics sells one that plugs in a USB port, and has the big advantage for me that it comes with a Linux Live-CD with all the programming tools on it. This way, I didn’t have to spend time to build my own developing environment. First I tested the web server, programmer and LiveCD on a real computer with an example from Tuxgraphics. After being satisfied that it worked, I created a virtual machine, booted from the LiveCD, configured networking and sshd and now I develop on that VM. But because it’s a LiveCD and settings are not persisted, I have to take a snapshot before shutting down the VM.
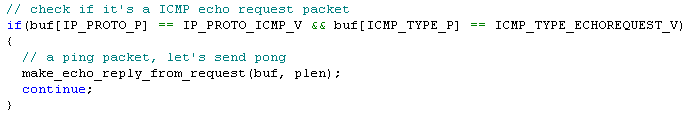
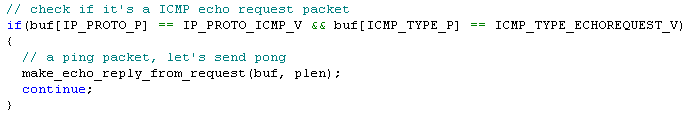
The board has an Ethernet controller, this means that you have to implement the IP functions you need in software on the AVR microcontroller. For example, to get a ping reply from the pocket server, you have to write code to identify the ICMP request, build the reply and transmit it, like this:
Likewise, you have to write code to handle ARP requests, which are essential for IP operation.
And for HTTP web serving, you have to implement TCP connections (e.g. SYN SYN-ACK ACK), parse the HTTP requests and send the corresponding replies. Building on Tuxgraphics’ example, I developed a simple framework to serve static and dynamic HTML pages. All is in the website array that is initialized in the InitWebsite function:

Use one entry per web page. The first pointer of each entry points to the URL you want to server, like /info.html. The second pointer is the content type, like HTML or plain text. And the third pointer points to the static content you want to serve. Set this pointer to NULL for dynamic content.
So if you just want to serve static pages for HTTP GET requests, modifying the code doesn’t require real programming skills. In the source code, just change the MAC address and IP address, redimension the website array and populate it with your pages.
But for dynamic pages, you’ll have to write a function that generates the dynamic content, and call that function when the dynamic page is requested:

In this example, we check if the index of the requested page (iHTTPURL) equals the index of the status.html page (URL_STATUS). If it does, we call the MakeStatusResponse function that will generate the web page displaying a counter.
You have to realize that this is a very basic HTTP server. It doesn’t keep state for the connections and it’s not multithreaded. If you need a more robust embedded web server, there are solutions like the FOX Board, it runs the BOA web server under Linux.
Download:
eicar.tar.gz (https)
MD5: A8D42CA6628A699C4C76A8412639CEDF
SHA256: 20760F7085830C73BBAE4C1D962D625429920079EFD9A5F38372953B1B5C7896
Untar and make. To program the mini AVR web server: make load_eicar