When I found a malicious script riddled with 0x00 bytes, SANS handler Bojan Zdrnja explained to me that this was an old trick. When rendering an HTML page, Internet Explorer will ignore all zero-bytes (bytes with value zero, 0x00). Malware authors use this to obscure their scripts. But this old trick still packs a punch.
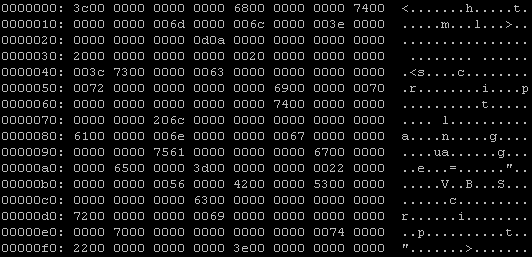
This is how the script looks in vi:

Maybe this hex dump makes it more clear to you:
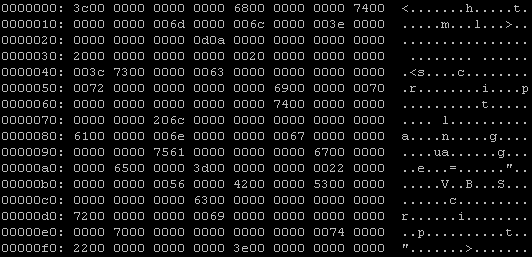
Recognize <html> <script…?
Well, a lot of AV programs are still fooled by this trick, VirusTotal reports that only 15 out of 32 AV products detect this malicious script.

When I remove all obscuring zero-bytes from this script, things get better: 25 out of 32 AV products detect it.
But what happens when I add more zero-bytes to the script?
Even more AV are fooled! Gradually adding more zero-bytes makes the detection ratio go down.
And at 254 zero-bytes between the individual characters of the script, McAfee VirusScan is the only AV to still detect this obscured script. One byte more (255 zero-bytes), and VirusScan doesn’t detect the script anymore. No AV on VirusTotal detects this malware obscured with 255 zero-bytes (or more). But for IE, this obscured HTML poses no problem, it still renders the page and executes the script.
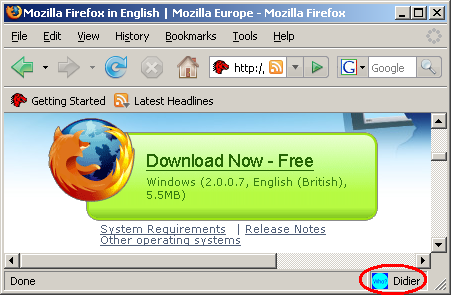
But you cannot rely on VirusTotal results alone. Modern AV products do not solely rely on file scanning to identify malware, they come with many techniques. For example, VirusScan has a feature called ScriptScan, a utility that intercepts all script execution requests to the MS scripting engines (VBS & JS). Since IE sends the malicious script stripped of its zero-bytes to the VBS scripting engine, ScriptScan has no problem detecting the malware and prevents its execution.
As it is the first time I get such a clear example of ScriptScan in action, I’ve made a screencast (YouTube) of it, XviD hires here.