This is a bug fix version for my nsrl.py script, a tool to check hashes with the NSRL list.
nsrl_V0_0_4.zip (http)MD5: 6F72B03493C73E88CB3771C860BC76D0
SHA256: D68039B8654C1D52CD1C12670C7E885E462B72BF23892E86BE86E6381C95B669
This is a bug fix version for my nsrl.py script, a tool to check hashes with the NSRL list.
nsrl_V0_0_4.zip (http)New features:
This new version brings extra statistics with option -f (fullread): counter for unique bytes, control bytes, printable bytes, high bytes. And lengths of the longest ASCII string, ASCII hexadecimal string and ASCII base64 string.
Remark that no check is made for hex string length being a multiple of 2 and base64 string length being a multiple of 4.
Rule DMP for minidumps was added.
And option -e now accepts multiple extensions (comma separated).
FileScanner_V0_0_0_8.zip (http)This new tool, teeplus.py, is an extension of the tee command.
The tools takes (binary) data from stdin, and sends it to stdout, while also writing the data to a file on disk.
While the tee command requires a filename as argument, teeplus.py takes no arguments (only options).
By default, teeplus.py will write the data to a file on disk, with filename equal to the sha256 of the data and extension .vir.
And it will also log this activity in a log file (teeplus.log by default).
Here is an example.
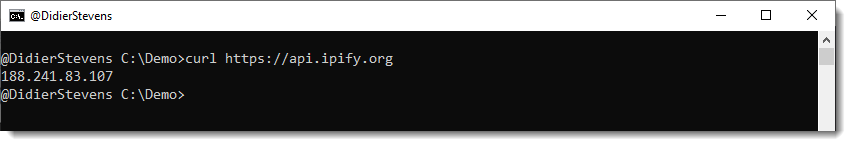
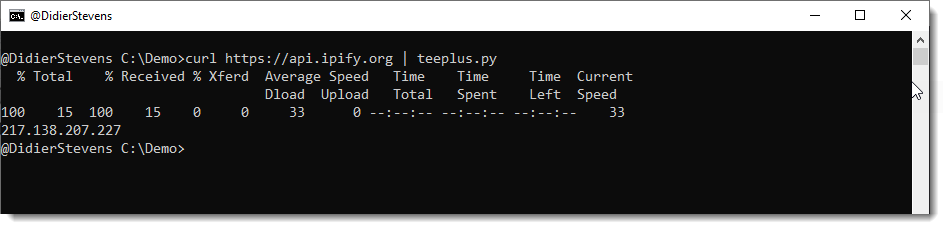
I run curl with a request to ipify to get my current public IPv4 address:
Then I pipe this output to teeplus.py:
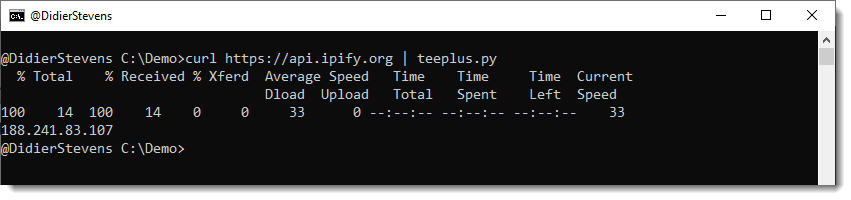
This results in the creation of two files inside the current directory:

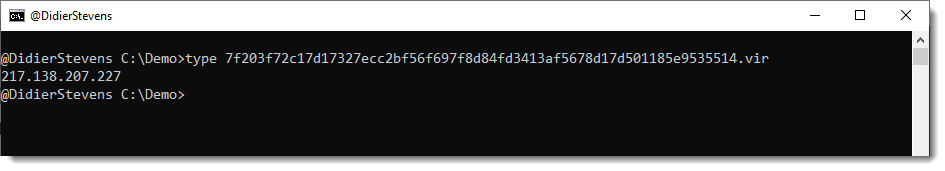
The first file it the output of the curl command:
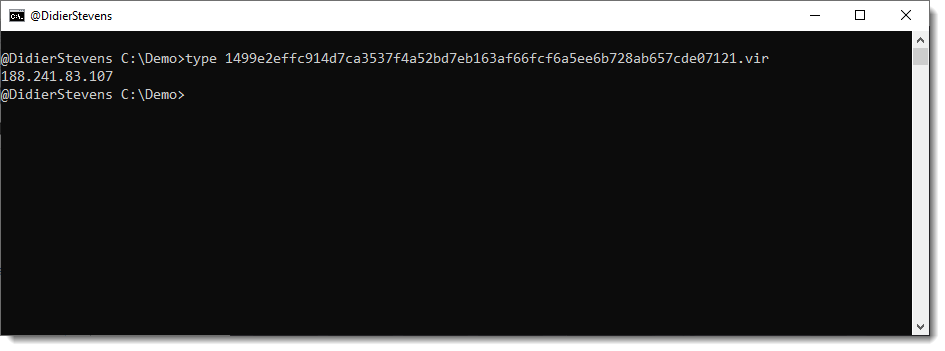
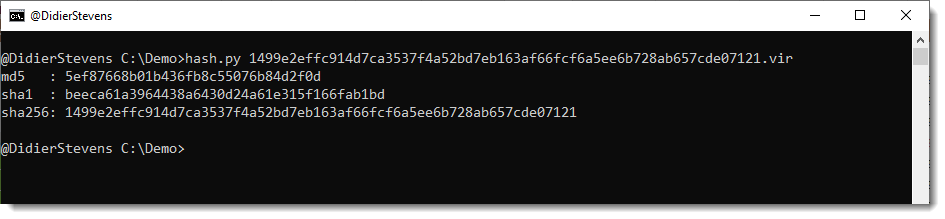
The filename is the SHA256 hash of the data with extension .vir:
The second file, teeplus.log, is a log file:
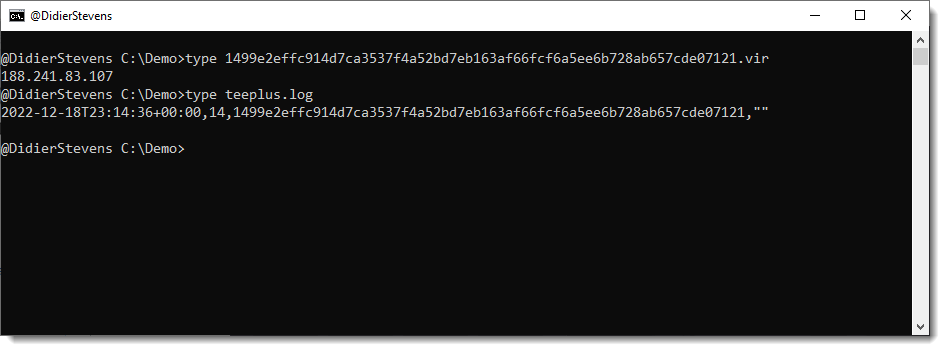
Each line in teeplus.log has 4 fields (comma separated):
A line is created for each invocation of the teeplus.py command:

When the IPv4 address changes:
And the command is executed again, a new .vir file is created (since the received data changed):
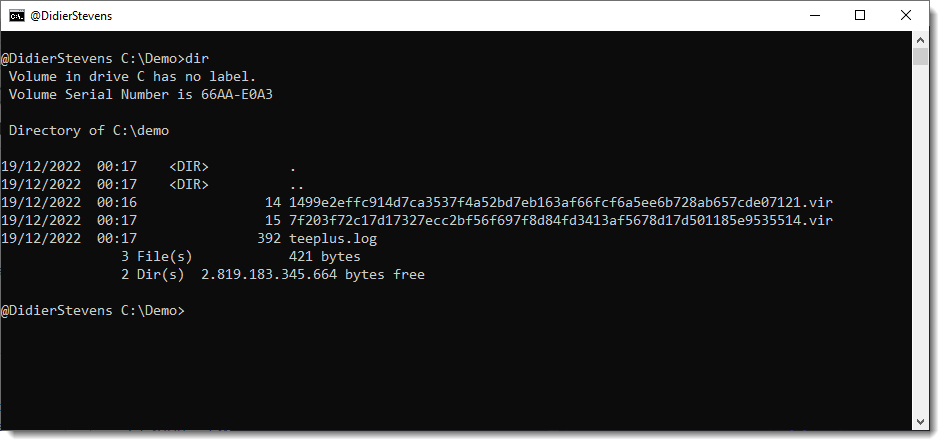
And this is reflected in the log file:
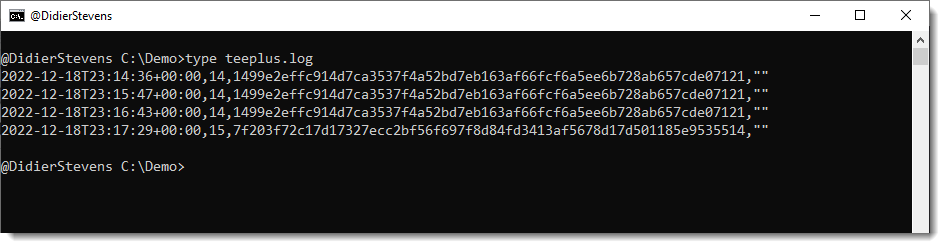
This allows you to create a log of your public IPv4 address, for example (by scheduling this command as a recurrent task).
I use it for monitoring websites, and saving a copy of the HTML page I downloaded. I will explain how in an upcoming blog post.
teeplus.py has a couple of options: you can change the extension of the saved file, and the filename of the log file. And you can also us option -n to prevent the data to be piped to stdout (or you could redirect to /dev/null).
This is something I would do when the teeplus.py command is not followed by another command.

Option -W can be used to write all files to disk. The only accepted value for -W is vir (for the moment). When this option is provided, all files are written to the local disk (ignoring contained paths) with their original name, and appended extension .vir.
To print out properties line per line, use separator *.
And more parsing for PK records has been added (with option -f). This is a work in progress, more info will provided in an upcoming blog post.
zipdump_v0_0_23.zip (http)This update to virustotal-search brings new options:
Options validate and skip support here files now.
And when validating hashes, a summary is displayed at the end of the report.
hash_V0_0_9.zip (http)This update to count.py, my tool to count items, adds totals and options for:
A colleague asked me for help with extracting code signing certificates from malicious files, to add them to Defender’s block list.
The procedure involves right-clicking the EXE in Windows Explorer, selecting properties to view the digital signature, and so on …
But I don’t like procedures where one has to click on malware.
So I looked for a PowerShell command, and found this.
Get-AuthenticodeSignature .\malware.exe.vir | Select-Object -ExpandProperty SignerCertificate | Export-Certificate -Type CERT -FilePath SignerCertificate.cer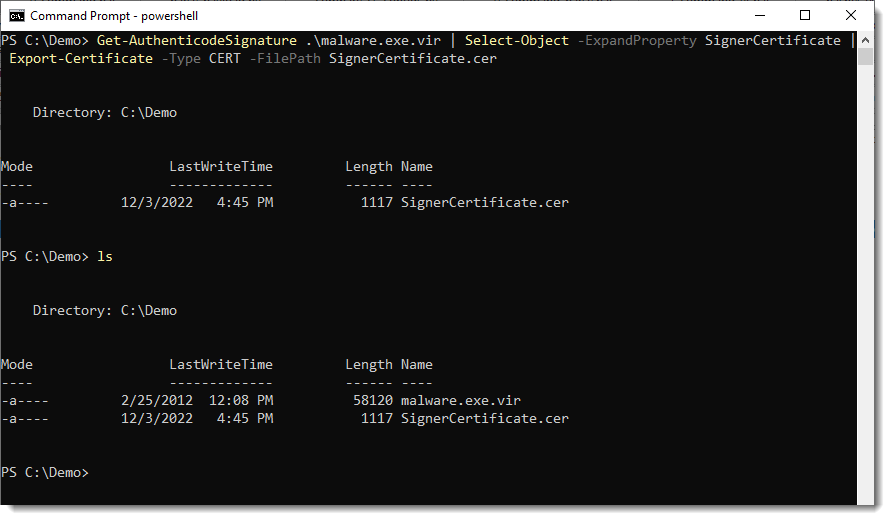
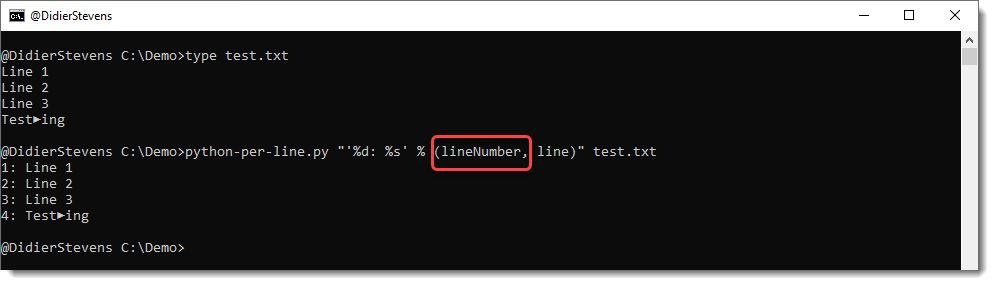
This is a small update to add the lineNumber variable.