Gmail identified the Fake CNN Alerts as SPAM from the beginning, but now warns against phishing too:

Gmail identified the Fake CNN Alerts as SPAM from the beginning, but now warns against phishing too:

Fake CNN alerts galore!
I seize the opportunity to publish a new video (warning: 8 minutes of command-line staring) (hires XviD version here) showing you how to use my tools to retrieve malware samples hosted on a website. If you just visit an infected website with Internet Explorer, you run the risk of infecting your machine. The safe way to retrieve samples is to work in a low-risk environment (e.g. non-root account on a Linux VM) and use tools that are unlikely to be the target of exploits hosted on said website.
The following tools are featured in the video:
The file numbering trick (01., 02., 03., …) allows me to document exactly how I obtained the sample.
Since I recorded the video, the malware seems to have been removed from the site. But be careful, it’s not uncommon that compromised websites get reinfected.
Here’s a new social engineering trick I hadn’t seen in my spam mail before:
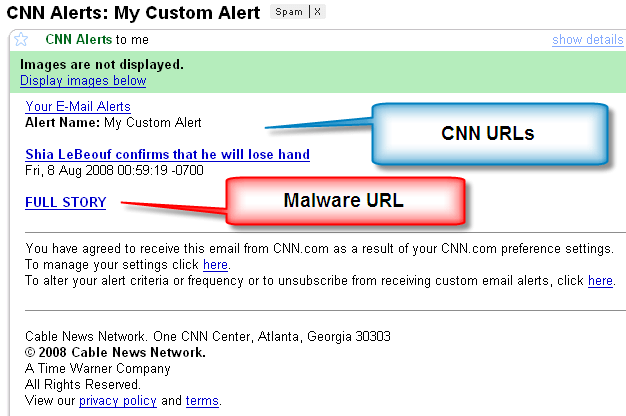
The Shia link actually points to a real CNN article about the olympics & terrorism. So you might be inclined to click on the full story link.
Like the CNN Top 10 malware, it has a fake Flash update:

Which happens to be malware.
I release USBVirusScan version 1.7.2.
Two new features:
-s scan available removable drives when USBVirusScan is started
-r also start the command at drive removal, parameter %e indicates drive arrival ‘A’ or drive removal ‘R’
Download:
USBVirusScan_V1_7_2.zip (https)
MD5: BDEF7BAE13C10B2B6CD650A89FD910ED
SHA256: 0090C73D6A3725E75C3388387A7A9E869C5D6BEA83E0D4D612E1CB25458163F3
My new stickers arrived today:

From now on, winners of my little puzzles can expect a little prize (I’ll contact winners of past puzzles)…
Ryan Goodings suggested I modify the header (starting_frequency and readings_per_sweep) of a band-pass filtered wsr file, to have Chanalyzer scale the filtered section. Here is the new version (use option –reduce), and this is the result:

Another WiFi program: wsrtool.py This Python program allows you to process wsr files (capture files of the ISM spectrum, created by Chanalyzer with a Wi-Spy adapter).
The tool filters out selected frequencies or amplitudes (band-pass and band-stop filter).
You need to install the Python module Construct.
Here’s an unfiltered capture:

And here I used a band-pass filter with cutoff frequencies 2420 MHz and 2445 MHz:

Here’s a new puzzle, and “by popular demand”, it’s a couple of magnitudes harder than previous puzzles.
The puzzle is a Windows console application, you can download it here. When you run the program, it prints “Authenticode Challenge version 1” to stdin. The challenge is twofold:
1) make the program print “Authenticode Challenge version 2” (that’s easy)
2) update the digital signature to keep it valid (not so easy)
When you check the digital signature of the puzzle, you’ll see this:

And after you changed the program to print “Authenticode Challenge version 2”, you’ll see an invalid signature:

The challenge is to keep the signature valid, using a certificate with the same public key.
All the data you need from me is in the executable. You’re not allowed to hack my servers in search of the private key.
FYI: this puzzle was reviewed by a PKI expert, who confirmed the solution.
Good luck, I hope there will be many challengers, and better yet, with another solution than mine!
I’ve updated my WhoAmI? Firefox add-on for version 3.
You can download it here or get it from the Mozilla site. It has remained in the Sandbox since my first post, but now I’ve nominated to leave the Sandbox. If you use it, please post a review on the Mozilla page to help it on its way out of the the Sandbox (or keep it there if it’s too buggy).
And now for the little puzzle: what is special about this other version of my WhoAmI? add-on?
So don’t get confused by these 2 versions: