This new version of USBVirusScan adds a switch (-q) to stop a running instance of USBVirusScan.
The program can be found here.
This new version of USBVirusScan adds a switch (-q) to stop a running instance of USBVirusScan.
The program can be found here.
Apple has released a new QuickTime version (7.1.5) without support for JavaScript. This happened about a week before I posted “P0wned by a QT movie”. I had analyzed the infection and written (but not published) my post before Apple published the update, and since I don’t use QT (it’s not installed on my systems), I was not aware of this fix when I published my post.
This unfortunate timeline created some confusion, several readers wanted to know if this infection vector could still be used with the latest QuickTime version. I’ve tested this and I can confirm that the latest version of QuickTime (7.1.5) doesn’t support JavaScript anymore. Apple has done the right thing, even if it was “a feature and not a bug”, the best thing to do was to remove support for JavaScript in QuickTime.
The modified QT movie I used in my tests displays a message box when it is embedded in an HTML page and viewed with IE. If you’re interested, I’ve made a movie of my tests (rest assured, it’s not QT), the movie is hosted here on YouTube, and you can find a hires version (XviD) here.
USBVirusScan v1.4.0 has a new “feature”: from this version on, only one instance can be running. This was requested by Alfredo.
I use a mutex to detect if an instance of USBVirusScan is already running, and if it is, I do not launch another instance.
Mutexes are used by programmers to orchestrate exclusive access to a resource. Suppose your program is multi-threaded and that separate threads are reading, checking and updating the same global variable. Thread A could read global variable G, followed by thread B writing global variable G. Thread A will then make decisions on an outdated value of global variable G (it has just been changed by thread B). To avoid this, we must be sure that reading, checking and updating is an atomic operation, i.e., that when thread B is using global variable G, threat A cannot start using it before thread B is done.
This can be done with a mutex. When thread B wants to use global variable G, it first has to create a mutex. Creating a mutex is requested to the OS. The OS guarantees that creating the mutex is also an atomic operation: 2 programs cannot create the same mutex simultaneously. If the mutex doesn’t exist, it is created and the program is informed of the creation. On the other hand, if the mutex already exists, the program is informed that the mutex already exists. So if thread B successfully creates the mutex, it knows that no other thread is using the global variable and that it can use it. If thread A tries to create a mutex, it will fail because it already exists, and therefor it knows it cannot use global variable G. When thread B has done reading, checking and writing global variable G, it releases the mutex, thereby giving other threads the opportunity to create the mutex and access global variable G.
A mutex can also be used to restrict the number of running instances of a program. When the program is started, it first creates a mutex. If it succeeds, it continues and never releases the mutex (the mutex will be released by the operating system when the program terminates). However, if the creation fails, the program knows that another instance is already running and it just stops. This makes that only one instance of the program can be running.
Mutexes can be named, for example “USBVirusScan”, this allows for the creation of many different mutexes.
Mutexes are also used by virus writers to limit the number of running instances of their virus. If a virus is allowed to reproduce uncontrolled on a machine, the huge number of running instances would soon kill the machine, thereby DoSing it.
Do you remember “inoculation” programs? They would prevent the execution of a particular virus strain on your machine. They work with mutexes: the inoculation program creates the same mutex as the virus would, and then stays resident, never releasing the mutex. If the virus wants to run on your inoculated machine, if fails to create the mutex and stops the infection, assuming your machine is already infected.
This tactic is also used in some viruses to disable competing viruses: not only do they create their own mutex, but also the mutex of the competing virus …
A few days ago I Googled again for Vanderelst Chauffagiste (Google and the Drive-by Download), I noticed the Spamdexing “R” Us site has disappeared from the SERPs. But it still exists.
This is an unexpected result of my post Google and the Drive-by Download:
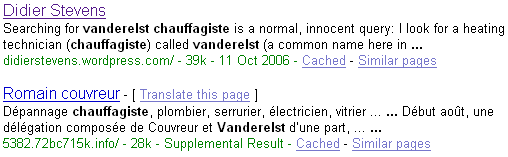
At the end of my post Google and the Drive-by Download, I wondered how prevalent such query results were.
This is an attempt to answer this question.
Here’s a Perl script that will execute Google queries and look for suspect URLs in the first page with a regular expression (remember, suspect URLs are of the form 123.1a2b3c.info). If you want to use the script on your Windows machine and don’t have a Perl interpreter, you can use ActiveState’s free ActivePerl.
Since I have no list of common Google queries used here in Belgium, I included a simple algorithm in my program to generate its own queries. They look like this: name profession. I feed my program with a list of frequently occurring last-names in Belgium and a list of professions you might want to search for (like a plumber).
Here’s the output of my program:
Suspect queries: 613.6x2q1y.info http://www.google.be/search?hl=fr&q=Thys+Blanchisseur 4859.4rhw0hk.info http://www.google.be/search?hl=fr&q=Gerard+Plombier Suspect URLs: 4859.4rhw0hk.info 613.6x2q1y.info 2 suspect queries out of 2322 queries (0.0861326442721792%).
About 1 out of 1000 queries (looking for a profession) list a drive-by download site on the first result page. That’s not too bad, but still a surprising result to me.
I’ve enhanced my UserAssist utility. After I published my utility, I had do to a small forensic investigation, but I couldn’t install my program on the machine. That’s why I added a feature to import from a REG file.
The treeview has been replaced with a table that also displays the session ID, counter and last timestamp of each entry.
The commands are in a pull-down menu:
New commands:
The about dialog contains a help section.
I posted my program (source code and binaries) here on the gotdotnet site. Download the ZIP file, you’ll have to extract UserAssist\UserAssist\bin\Release\UserAssist.exe to get my program. There is no setup, it’s just one executable. You’ll need the .NET Framework 2.0 runtime to run my program (download it only if you have a problem running my program, if you have an up-to-date version of Windows XP, the .NET 2.0 Framework will already be installed).
Chris explains how to recover the Safeboot key with a Live CD directly from the System Volume Information directory: Repairing Safe Mode (Safeboot)
Clever idea Chris!
Ryan was inspired by my post Viewing strings in executables and explains how to unpack Packed Executables.
Good work Ryan!