This new version brings a bug fix and an update to plugin_biff’s XOR deobfuscation.
oledump_V0_0_62.zip (https)MD5: F16DB945970B49A60155443ED82CDE29
SHA256: 4AE5DF2CC8E8F5A395027A8056B1A33B8F05C0AB6FC18D56D46DC151BB4302FB
This new version brings a bug fix and an update to plugin_biff’s XOR deobfuscation.
oledump_V0_0_62.zip (https)This new version of base64dump.py brings bug fixes and support for BASE85 RFC 1924 encoding.
If you want to know how I go about adding a new decoding to base64dump.py, watch this video:
Here is version 0.0.0.15, with bug fixes but without base85:
base64dump_V0_0_15.zip (https)And here is version 0.0.0.16 with base85:
base64dump_V0_0_16.zip (https)This new version of FileScanner brings bug fixes and new features, like UNICODE filename support and an embedded man page.

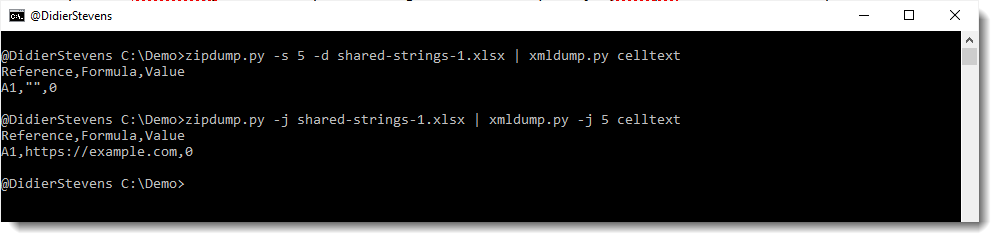
This update to xmldump.py, a tool to help with viewing XML files, adds option -j (–jsoninput) to handle JSON output produced by zipdump.py.
With this option, shared strings from OOXML spreadsheets will be used with command celltext.
I will explain more in an upcoming blog post.
This new version of oledump.py comes with Excel 4 formula parsing improvements in the plugin_biff plugin.
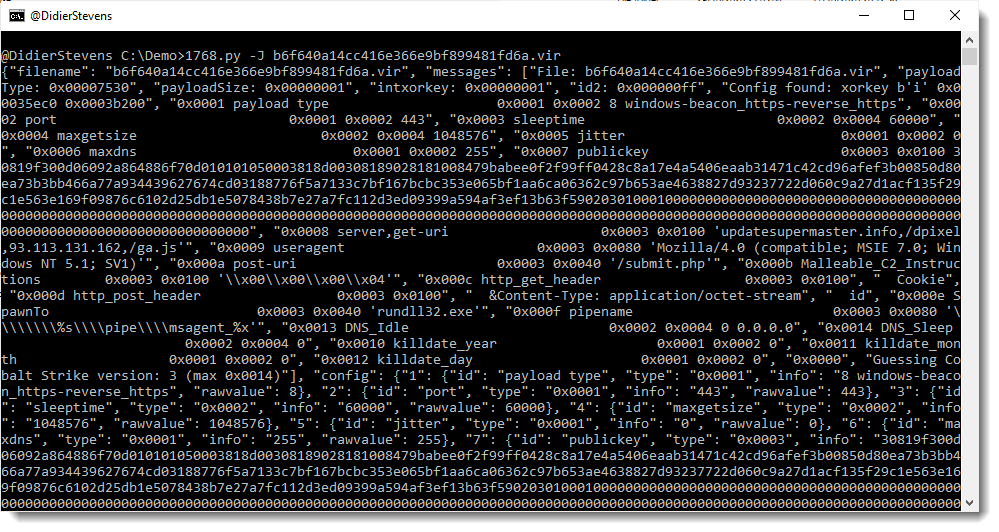
oledump_V0_0_61.zip (https)There are no code changes to this version of 1768.py, my tool to analyze Cobalt Strike beacons.
What is new, is file 1768.json: this file contains statistical data for license IDs.

Over a period of one month, I collected license ID information from these sources: threatviewio and @cobaltstrikebot.
For each license ID that is found on more than one IP address / hostname, I include simple statistics: the number of unique IP addresses / hostnames and the number of unique public keys.
When analyzing malicious Cobalt Strike beacons, I often see recurring license IDs. That’s why I decided to add logic and a JSON file to my tool, with license IDs I’ve seen before. And now this has evolved to a small repository of often seen license IDs.
Here is an example with a sample we discussed on the Internet Storm Center diary:

The license ID is 1873433027 and this ID is associated with 18 unique IP addresses / hostnames, and 15 unique public keys. This is a clear indication that this license ID is used by malicious actors. License IDs that have been seen only once, could belong to red teams, that is why they are not included in file 1768.json. The more often a license ID is seen, the higher the chance it is used by malicious actors. Of course, it is not excluded that there are legitimate license IDs from red teams in this list, but I expect they will have low frequencies.
Takeaway: if your sample has a license ID that appears in 1768.json, then it has been seen before (at least twice), and you’re likely not dealing with a pentest.
1768_v0_0_7.zip (https)Here is an update to my Python templates.
I use these templates as a starting point for new tools or for quick development of ad-hoc tools.
I also recorded a video showing how to use my template to create your own tool: ssdeep Python Example Based On My Templates.
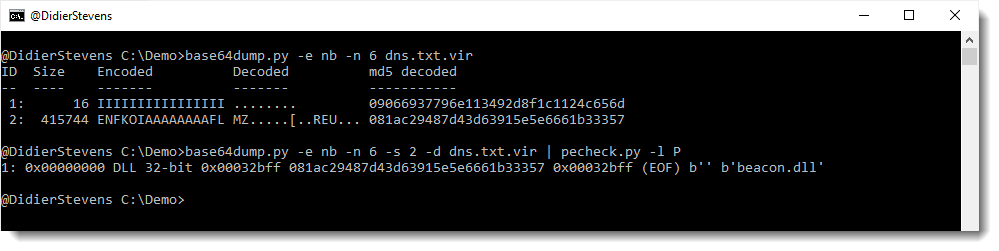
python-templates_V0_0_5.zip (https)This new version of base64dump.py supports a new encoding: NETBIOS Name encoding.
NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used.
I encountered this in DNS TXT records of a Cobalt Strike DNS stager. More on that later.
This new version of re-search.py adds gzip support and filtering of private IPv4 addresses:

This new version of 1768.py, my tool to analyze Cobalt Stike beacons, has fixes, support for more encodings, and an option to output the config in JSON format.