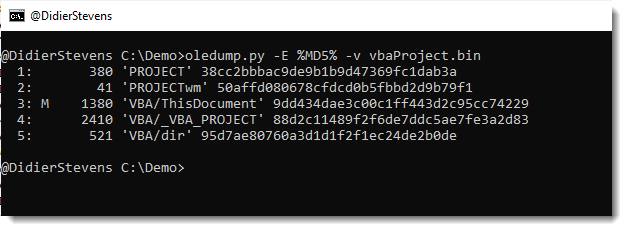
This is a bug fix update for oledump.py.
It fixes a bug that occurred when you calculated the hash of decompressed VBA code:
MD5: 52440972347843FF56B8F754910BFE4A
SHA256: F92660FFA0F484B46A14944A8B7B475C3D34E80D9C197FA1E99C444CA9ED533B
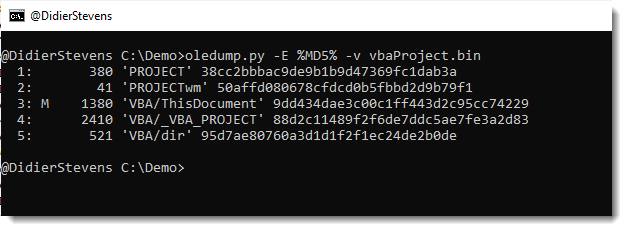
This is a bug fix update for oledump.py.
It fixes a bug that occurred when you calculated the hash of decompressed VBA code:
This Python script is essentially a wrapper for the smtpd Python module.
I use it to receive emails, and write them to disk.
Sometimes I use this to exfiltrate (malicious) emails.
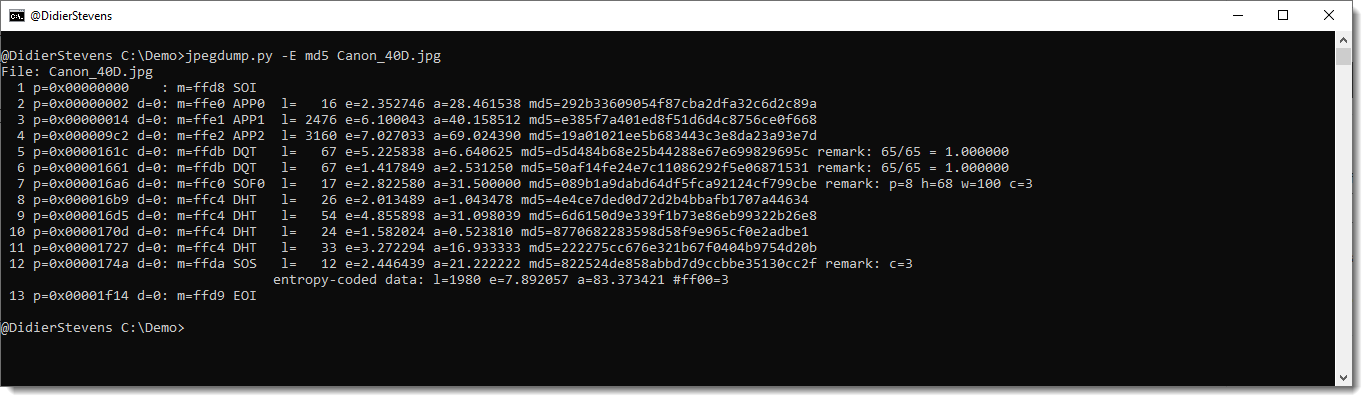
This new version of jpegdump.py adds option -E to display extra info for each segment.
This extra data is a hash of the segment’s data: md5, sha1, sha256.
This new version brings a new encoding: zxcn
zxcn stands for “zero x comma no-leading zero”, and is very similar to zxc encoding (zero x comma).
Example of zxc: 0x90,0x0A,0x4D,0x5A
Remark the leading zero for value 0x0A (values smaller than 0x10).
With zxcn encoding, there is no leading zero for values smaller than 0x10.
Thus the example for zxcn becomes: 0x90,0xA,0x4D,0x5A
base64dump_V0_0_20.zip (https)This new version of pecheck adds support for dumping files (-D) while using option -l P.
pecheck-v0_7_14.zip (https)This new version brings some options to guide the XOR-key detection algorithm.
The beacon’s AES and HMAC key are contained in writable process memory: my tool cs-extract-key.py can detect these keys. But the beacon can be configured to encode these keys while it is sleeping. This feature is called a sleep mask, and uses a 13-byte long XOR key. The complete writable memory section that contains the beacon process data, like encryption keys, is encoded with this 13-byte long XOR key.
Since writable process memory sections contain a lot of consecutive NULL bytes (0x00), the 13-byte long XOR-key will be present in the encoded process memory (XORing 0x00 with a key gives the key).
My tool will try to detect this XOR-key, but searching for 13-byte long random byte sequences that appear often. It does this by considering all possible 13-byte long sequences as a potential key, and counting how many times each potential key appears. Then it throws away all keys that don’t appear often (less than 100 times) and all keys that do not appear random (for example, keys with more than 3 0x00 bytes).
The most prevalent of these remaining keys, is considered as the most likely XOR key.
The new options that have been added to version 0.0.3, allow to guide this key finding algorithm.
Option –keysize is the XOR key size: the default value is 13.
Option –numberofkeystotry specifies how many keys that are considered to be potential XOR keys. The default value is 10: this means that the 10 most prevalent keys are selected and displayed.
Option –keystotry specifies which keys to try, out of the 10 keys selected. By default, only the first key (most prevalent key) is tried: value 0. But you can provide several keys, as a comma separated list of indices.
A potential XOR-key is selected as a decoding key, if the decoded memory section contains string b’sha256\x00′.
Finally, option -r can be used to let the tool analyze a raw set of data (e.g., the provided file is not parsed as a minidump file, but just taken as raw data).
cs-analyze-processdump_V0_0_3.zip (https)I added option –donotfullsearch in this new version of my tool to extract encryption keys from process memory dumps of beacons.
When this option is used, cs-extract-key.py will not fall back to a full search when string sha256\x00 is not found.
cs-extract-key_V0_0_4.zip (https)1768.py, my tool to analyze Cobalt Strike beacons, has an update: updated statistics and support for your own, private 1768.json file: 1768b.json. When 1768b.json exists, it is used by 1768.py in stead of 1768.json.
1768_v0_0_11.zip (https)This update for cs-parse-traffic.py, my tool to parse/decrypt Cobalt Strike network traffic, includes bug fixes and new definitions.
cs-parse-traffic_V0_0_4.zip (https)This is a bugfix version.
cs-decrypt-metadata_V0_0_4.zip (https)