- MiTM Cobalt Strike Network Traffic
- Update: base64dump.py Version 0.0.19
- Update: cs-decrypt-metadata.py Version 0.0.4
- Update: cs-parse-traffic.py Version 0.0.4
- Update: 1768.py Version 0.0.11
- Update: cs-extract-key.py Version 0.0.4
- Update: cs-analyze-processdump.py Version 0.0.3
- VBA: __SRP_ Streams
- Update: pecheck Version 0.7.14
- Update: base64dump.py Version 0.0.20
Saturday 1 January 2022
Overview of Content Published in December
Wednesday 1 December 2021
Overview of Content Published in November
Blog posts:
- New Tool: cs-extract-key.py
- Update: 1768.py Version 0.0.9
- Update: cs-decrypt-metadata.py Version 0.0.2
- Update: 1768.py Version 0.0.10
- Update: base64dump.py Version 0.0.18
- Update: cs-decrypt-metadata.py Version 0.0.3
- New tool: cs-analyze-processdump.py
- New Tool: cs-parse-traffic.py
- Update: cs-extract-key.py Version 0.0.3
- Decrypting Cobalt Strike Traffic With Keys Extracted From Process Memory
- Decrypting Cobalt Strike Metadata Without and With Malleable C2 Instructions
- Obfuscated Maldoc: Reversed BASE64
- YARA Rules for Office Maldocs
- Decrypting Cobalt Strike Traffic With Keys Extracted From Process Memory
- Decrypting Cobalt Strike Metadata Without and With Malleable C2 Instructions
- Obfuscated Maldoc: Reversed BASE64
- YARA Rules for Office Maldocs
- Decrypting Cobalt Strike Traffic With a “Leaked” Private Key
- Sysinternals: Autoruns and Sysmon updates
- Video: Phishing ZIP With Malformed Filename
- Decrypting Cobalt Strike Traffic With Keys Extracted From Process Memory
- Video: Decrypting Cobalt Strike Traffic With Keys Extracted From Process Memory
- Obfuscated Maldoc: Reversed BASE64
- Video: Obfuscated Maldoc: Reversed BASE64
- External Email System FBI Compromised: Sending Out Fake Warnings
- Backdooring PAM
- Simple YARA Rules for Office Maldocs
- YARA Rule for OOXML Maldocs: Less False Positives
- YARA’s Private Strings
- Video: SANS Holiday Hack Challenge 2021 Q&A with Ed Skoudis
- Video: YARA Rules for Office Maldocs
- Wireshark 3.6.0 Released
Monday 29 November 2021
New Tool: cs-parse-traffic.py
This tool is the combination of beta tool cs-parse-http-traffic.py (discontinued) and unreleased tool cs-parse-dns-traffic.py: it can decrypt and parse Cobalt Strike DNS and HTTP beacon network traffic.
By default it handles HTTP traffic. Use option -f dns to handle DNS traffic.
cs-parse-traffic_V0_0_3.zip (https)MD5: D11D64222CD77407FCEE5E6235470828
SHA256: 916B44513620FD2BB3F7263D279E8219419A87F89CDA1253011D7338896405DD
Wednesday 3 November 2021
New Tool: cs-extract-key.py
cs-extract-key.py is a tool designed to extract cryptographic keys from Cobalt Strike beacon process memory dumps.
This tool was already available in my beta repository.
This tool can extract cryptographic keys from process memory dumps of a version 3.x beacon directly:
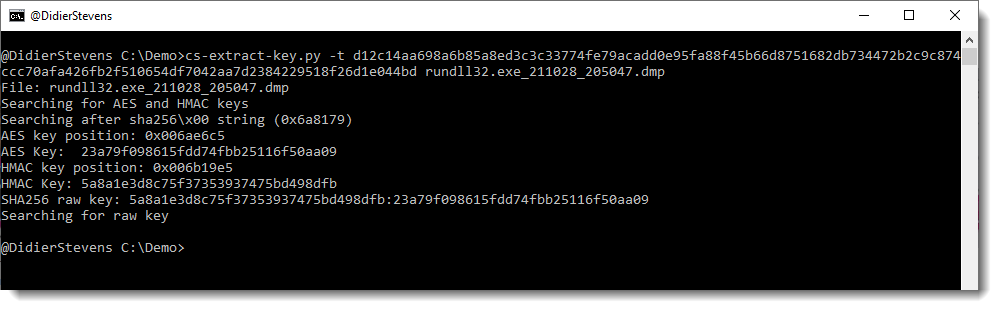
And from version 4.x together with encrypted data extracted from network capture:
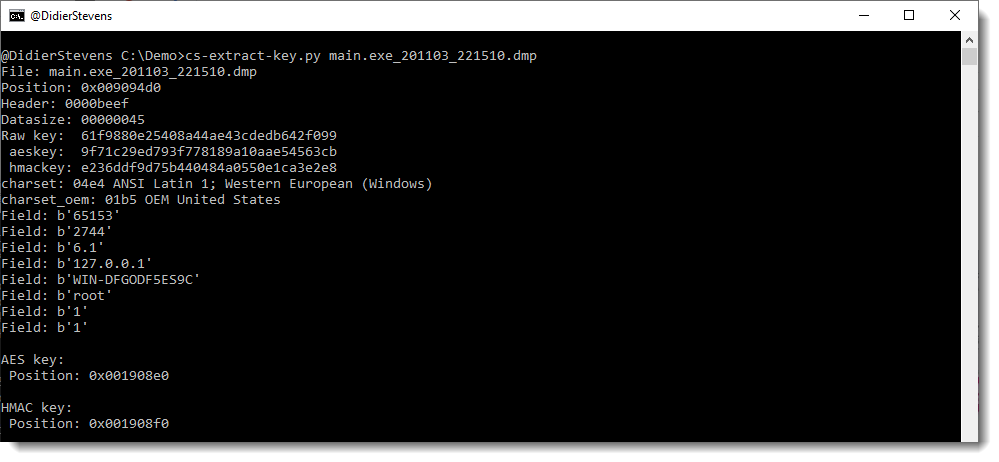
More details can be found in the man page, and in and upcoming blog post.
cs-extract-key_V0_0_1.zip (https)MD5: 4102A5A5BFD4D432DA4A721D43F568F5
SHA256: BBEDF6CBFFF51669187694F463C32A49F53420BEDF8B76508D06850643DE334F
Monday 1 November 2021
Overview of Content Published in October
Here is an overview of content I published in October:
Blog posts:
- New Tool: onion-connect-service-detection.py
- Update: 1768.py Version 0.0.8
- “Public” Private Cobalt Strike Keys
- New Tool: cs-decrypt-metadata.py
YouTube videos:
- CVE-2021-40444 Maldocs: Extracting URLs
- Cobalt Strike: Decrypting C2 Traffic With A “Leaked” Private Key
- Phishing ZIP With Malformed Filename
Videoblog posts:
- Strings Analysis: VBA & Excel4 Maldoc
- CVE-2021-40444 Maldocs: Extracting URLs
- Cobalt Strike: Decrypting C2 Traffic With A ?Leaked? Private Key
- Phishing ZIP With Malformed Filename
SANS ISC Diary entries:
- Video: CVE-2021-40444 Maldocs: Extracting URLs
- Wireshark 3.4.9 Released
- YARA Release v4.1.3
- Reader Malware: ZIP/HTML Phish
- Phishing ZIP With Malformed Filename
- Decrypting Cobalt Strike Traffic With a “Leaked” Private Key
- Sysinternals: Autoruns and Sysmon updates
- Video: Phishing ZIP With Malformed Filename
NVISO blog posts:
Friday 22 October 2021
New Tool: cs-decrypt-metadata.py
cs-decrypt-metadata.py is a new tool, developed to decrypt the metadata of a Cobalt Strike beacon.
An active beacon regularly checks in with its team server, transmitting medata (like the AES key, the username & machine name, …) that is encrypted with the team server’s private key.
This tool can decrypt this data, provided:
- you give it the file containing the private (and public) key, .cobaltstrike.beacon_keys (option -f)
- you give it the private key in hexadecimal format (option -p)
- the private key is one of the 6 keys in its repository (default behavior)
I will publish blog posts explaining how to use this tool.
Here is a quick example:

MD5: 31F94659163A6E044A011B0D82623413
SHA256: 50ED1820DC63009B579D7D894D4DD3C5F181CFC000CA83B2134100EE92EEDD9F
Saturday 2 October 2021
Overview of Content Published in September
Sunday 19 September 2021
Overview of Content Published in August
Monday 2 August 2021
Overview of Content Published in July
- Update: xmldump.py Version 0.0.7
- New Tool: texteditor.py
- Update: FileScanner Version 0.0.0.7
- New Tool: dnsresolver.py
- sysmon?s DNS QueryStatus Field
- Update: base64dump.py Version 0.0.16
- Using SeBackupPrivilege With Python