This is a bugfix version.
base64dump_V0_0_19.zip (https)MD5: 0D250DCB3FCE5D41A6FCB3AAD3937019
SHA256: FECA04873B87A15F0713938717611E86ED360F51AF28FCD03CEEFC4688BD7D67
This is a bugfix version.
base64dump_V0_0_19.zip (https)I made a small PoC. cs-mitm. py is a mitmproxy script that intercepts Cobalt Strike traffic, decrypts it and injects its own commands. In this video, a malicious beacon is terminated by sending it an exit command. I selected a malicious beacon that uses one of the leaked private keys.
The script does not support data transforms, but that can be easily added, for example with code found in cs-parse-traffic.py.
This update brings a new option: -V –verbose.
Verbose output includes an hex/ascii dump of the decrypted data:

This tool is the combination of beta tool cs-parse-http-traffic.py (discontinued) and unreleased tool cs-parse-dns-traffic.py: it can decrypt and parse Cobalt Strike DNS and HTTP beacon network traffic.
By default it handles HTTP traffic. Use option -f dns to handle DNS traffic.
cs-parse-traffic_V0_0_3.zip (https)This is cs-analyze-processdump.py, my tool to analyze Cobalt Strike beacon process dumps, detecting and decoding sleep mode encoding.
cs-analyze-processdump_V0_0_2.zip (https)This is a bugfix version of cs-decrypt-metadata.py, my tool to decrypt Cobalt Strike metadata.
cs-decrypt-metadata_V0_0_3.zip (https)This is a bug fix version.
base64dump_V0_0_18.zip (https)This new version of 1768.py, my tool to analyze Cobalt Strike beacons, adds some small changes, like extra tests and defines more field names.
1768_v0_0_10.zip (https)This new version of my tool to decrypt Cobalt Strike metadata, now supports transformations.
By default, encrypted metadata in Cobalt Strike traffic is encoded with BASE64 and then transmitted via the Cookie header in HTTP(S) requests.
This metadata is encrypted with a public RSA key, and can be decrypted if the private key is known.
Here is an example of a malicious beacon with a specific metadata encoding.
Analyzing the beacon with my tool 1768.py yields the following information:

First: a public key (field 0x0007) is used, for which we know the private key: thus we will be able to decrypt the metadata.
Second: the encrypted metadata has a specific encoding (field 0x000c). This beacon was configured with a profile that specifies that the encrypted metadata must be encoded with BASE64 URL-safe (this is a variant of BASE64, that uses characters – and _ in stead of + and /). Then it is prefixed with string __cfduid= and transmitted via the Cookie header.

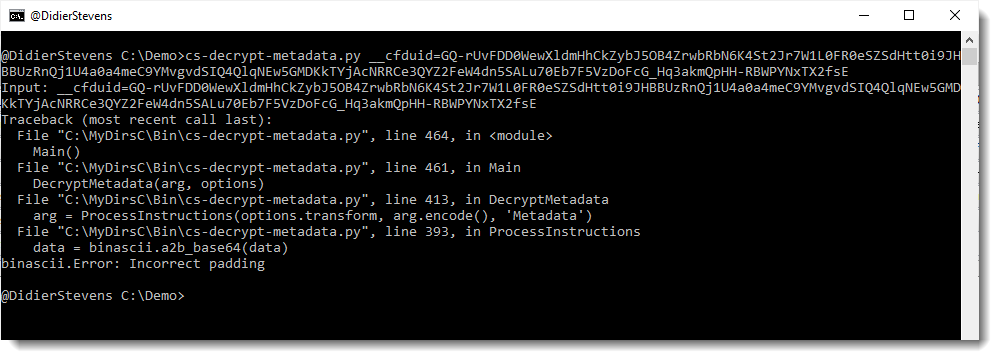
An error will result when this data is processed by tool cs-decrypt-metadata.py without providing the transformation instructions:
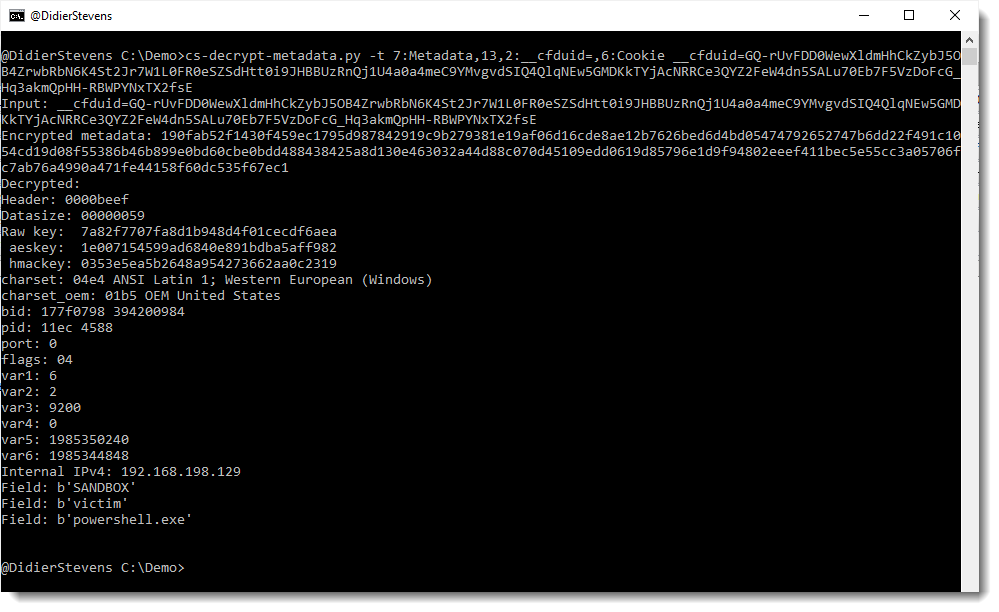
The following transformation instructions must be provided to properly decode and decrypt the metadata: 7:Metadata,13,2:__cfduid=,6:Cookie
This is done with option -t: