VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password.
Tools like oledump.py are not hindered by a VBA password, they can extract VBA code without problem, as it is not encrypted.
The VBA password is stored as the DPB value of the PROJECT stream:


You can remove password protection by replacing the values of ID, CMG, DPB and GC with the values of an unprotected VBA Project.
Thus a VBA password is no hindrance for staticanalysis.
However, we might still want to recover the password, just for the fun of it. How do we proceed?
The password itself is not stored inside the PROJECT stream. In stead, a hash is stored: the SHA1 hash of the password (MBCS representation) + 4 byte salt.
Then, this hash is encrypted (data encryption as described in MS-OVBA 2.4.3.2) and the hexadecimal representation of this encrypted hash is the value of DPB.
This data encryption is done according to an algorithm that does not use a secret key. I wrote an oledump.py plugin (plugin_vbaproject.py) to decrypt the hash and display it in a format suitable for John the Ripper and Hashcat:
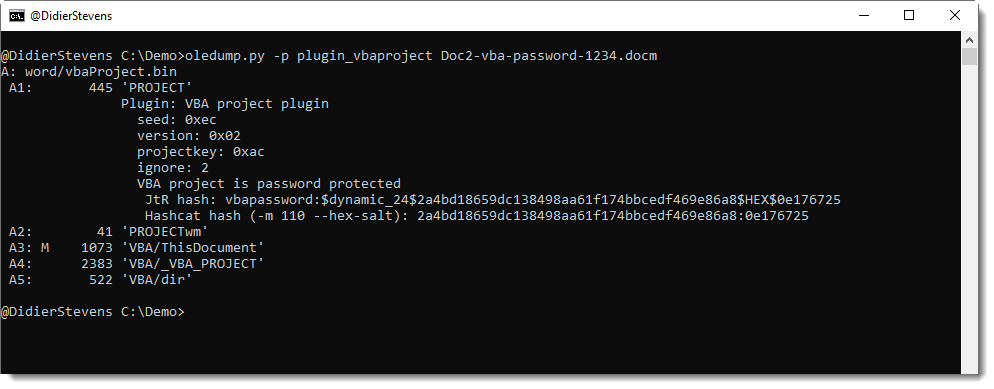
The SHA1 of a password + salt is a dynamic format in John the Ripper: dynamic_24.

For Hashcat, it is mode 110 and you also need to use option –hex-salt.

Remark that the password passed as argument to the SHA1 function is represented in Multi Byte Character Set format. This means that ASCII characters are represented as bytes, but that non-ASCII characters might be represented with more than one byte, depending on the VBA project’s code page.
Thank you, analysing several douzend MS Office malware from the Baazar there were several with VBA-password.
The following are interessting from my point of view: either for obfuscation or (my) difficuties to analyse:
docm: write MZ in memory
2deb003f7297cb6b40320e38aae81f62e338512bdf0acb27fb3ccdf7386b16aa
Heodo: docx,read PowerShell from Stream ‘o’, malformed zip
bf4fffe027c8d6b7f301f79506892c1666c59fbb0e01ee66e6326eae28c6c66d
PPT, the ony one of a serious with good obfuscation
9bd432d55037ffe62d2763a33bc1944be77cb4f31173ce5ea14f98c2dfa38665
xlsm: Obfuscation with rnd()
99842250e5da8f987227c22d864ea6552cbf176710cd5c45f430bc2765cbf534
xlsm, purged
966d24f3e5616ad72402614d846d892fd5756ade55219ca6f3a5440259fc8594
doc, Java-script
ddfedf6178d86d3372922620116d8c973e0627b5ac1ef087cc7c15cfcc452480
xlsx, sheet password: AAAABABABBAF, 6 shapes, no code visible with LibreOffice
b23aad76a523c780d42015490cff3209608454c016849f547e0584d78eaff4bb.xlsx
doc,Hyperlink
1cb15aebd509985de8a7792a474660cdecf8ab1cb008b86abcb3b5971b7a4480
xlsx, XMLHttp, url not readable
edbb25dfdfe594eb597484e31968fafa0462e81b203497aff0f5a60879860e53
xlsx, Magic-Bytes: d0cf 11e0 a1b1 1ae1, Sheet-password: AAAAAABAAABi, 6 Shapes, Where is the code?
7fa94fbd85d8ff81131e2a049e55df3b7805ad8e258974d47f360dbfb4ea03d9xlsx
docm, nice obfuscated
3d9ded92dc9eb820ef7ea68d7f844cd217b7dbebc643d58048565b922736b43f
Comment by No(anonym) — Friday 24 July 2020 @ 14:50
[…] that the VBA code itself is not encoded/encrypted, it is stored in cleartext (although compressed) [3]. When a document with a password protected VBA project is opened, the VBA macros will execute […]
Pingback by Epic Manchego – atypical maldoc delivery brings flurry of infostealers – NVISO Labs — Tuesday 1 September 2020 @ 11:33
Hi,
This is absolutely amazing work, I was wondering whether you have written or know of a way to do the same with MS Access?
Comment by Sudo_oth — Friday 5 March 2021 @ 14:46
No
Comment by Didier Stevens — Saturday 6 March 2021 @ 13:23
Thank you!
Comment by shigari — Sunday 23 May 2021 @ 19:26
Hi, do you know where the salt is stored / how it is generated? I’d like to produce this hash on my own to automate password protecting Excel macro files.
Thanks,
Michał
Comment by Anonymous — Monday 28 October 2024 @ 9:37
Take a look at the source code of the EPPlus library.
Comment by Didier Stevens — Wednesday 30 October 2024 @ 18:31