There are a couple of scripts and programs available on the Internet to extract the configuration of the Dyre banking malware from a memory dump. What I’m showing here is a method using a generic regular expression tool I developed (re-search).
Here is the Dyre configuration extracted from the strings found inside the memory dump:

I want to produce a list of the domains found as first item in an <litem> element. re-search is a bit like grep -o, it doesn’t select lines but it selects matches of the provided regular expression. Here I’m looking for tag <litem>:

By default, re-search will process text files line-by-line, like grep. But since the process memory dump is not a text file but a binary file, it’s best not to try to process it line-by-line, but process it in one go. This is done with option -f (fullread).
Next I’m extending my regular expression to include the newline characters following <litem>:

And now I extend it with the domain (remark that the Dyre configuration supports asterisks (*) in the domain names):

If you include a group () in your regular expression, re-search will only output the matched group, and not the complete regex match. So by surrounding the regex for the domain with parentheses, I extract the domains:

This gives me 1632 domains, but many domains appear more than once in the list. I use option -u (unique) to produce a list of unique domain names (683 domains):

Producing a sorted list of domain names is not simple when they have subdomains:
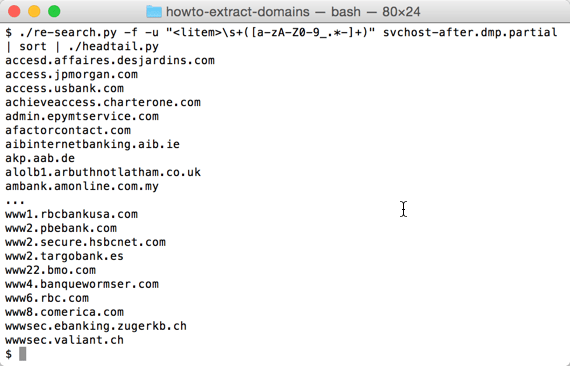
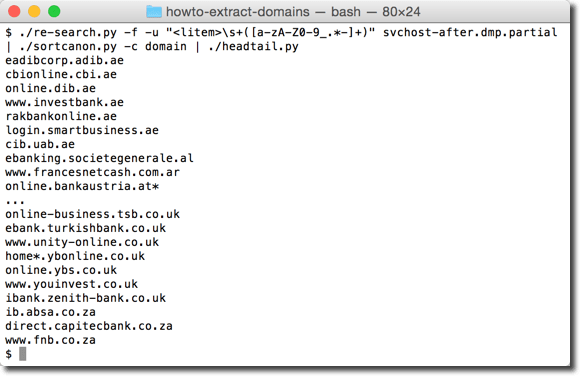
That’s why I have a tool to sort domains by tld first, then domain, then subdomain, …
re-search_V0_0_1.zip (https)
MD5: 5700D814CE5DD5B47F9C09CD819256BD
SHA256: 8CCF0117444A2F28BAEA6281200805A07445E9A061D301CC385965F3D0E8B1AF
[…] Extraire la configuration de Dyre depuis un dump mémoire (Didier Stevens) […]
Pingback by Newsletter 100% Sécurité Informatique semaine 28 - Adacis — Wednesday 15 July 2015 @ 8:51