XORStrings is best described as the combination of my XORSearch tool and the well-known strings command.
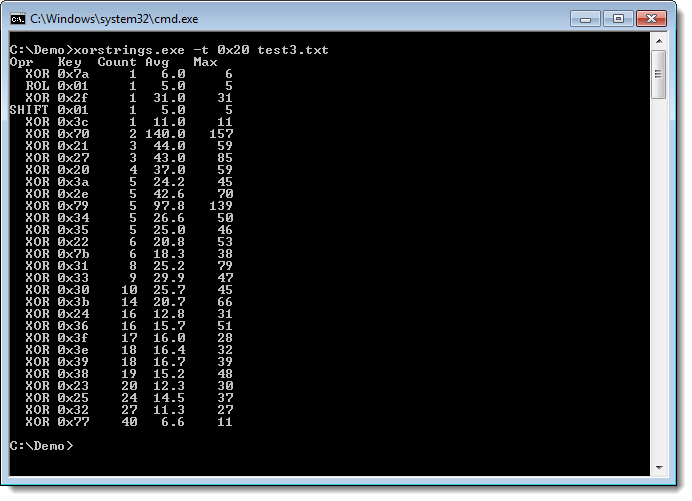
XORStrings will search for strings in the (binary) file you provide it, using the same encodings as XORSearch (XOR, ROL, ROT and SHIFT). For every encoding/key, XORStrings will search for strings and report the number of strings found, the average string length and the maximum string length. The report is sorted by the number of strings found, but can also be sorted by the maximum string length (use option -m). By default, the string terminator is 0x00, but you can provide your own with option -t, like the space character (0x20) in this example:
I’ve used XORStrings to identify the encoding used in TeamViewer traffic.
There are more options than the ones I mentioned here. I’ll create a dedicated page for this tool, but for now, I invite you to discover the options yourself.
XORStrings_V0_0_1.zip (https)
MD5: 27DA0B3BC5296179CB58181BDFF99F8D
SHA256: 5EA7E063A41E38E9E6277F1CD73FCEA2AEF50C33C44D75C226900314FF84A1B5