It seems that each time I attend Black Hat, I get some new steganography idea.
It’s easy to hide data inside the Wikipedia pages. But before I explain how, understand that the general principle of what I will explain applies to most sites where users can edit content. They can all be used as a covert channel, but Wikipedia has become so common that it would have passed under my radar when performing a forensic investigation. But not anymore.
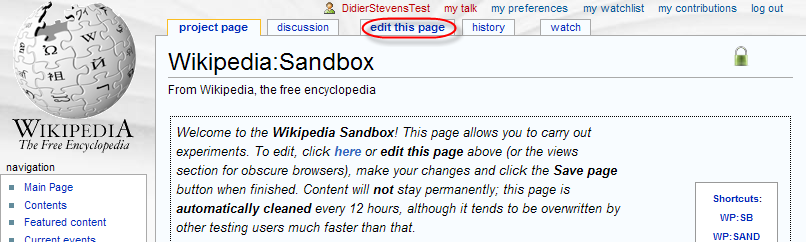
You can use the Wikipedia Sandbox to experiment while avoiding the wrath of the Wiki gods.
Select the edit this page tab to start editing the article:
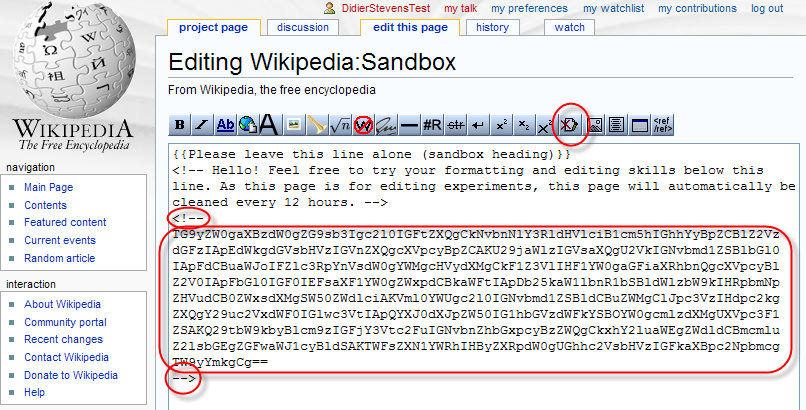
Prepare the data you want to store on Wikipedia by converting it to a base64 representation (you can ZIP and/or encrypt it before converting it to base64). Insert the base64 data as a hidden comment inside the page:
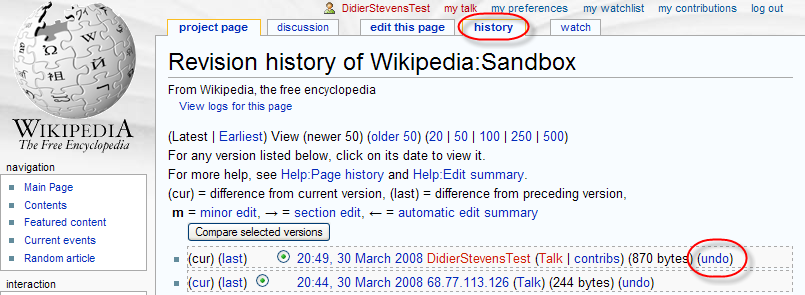
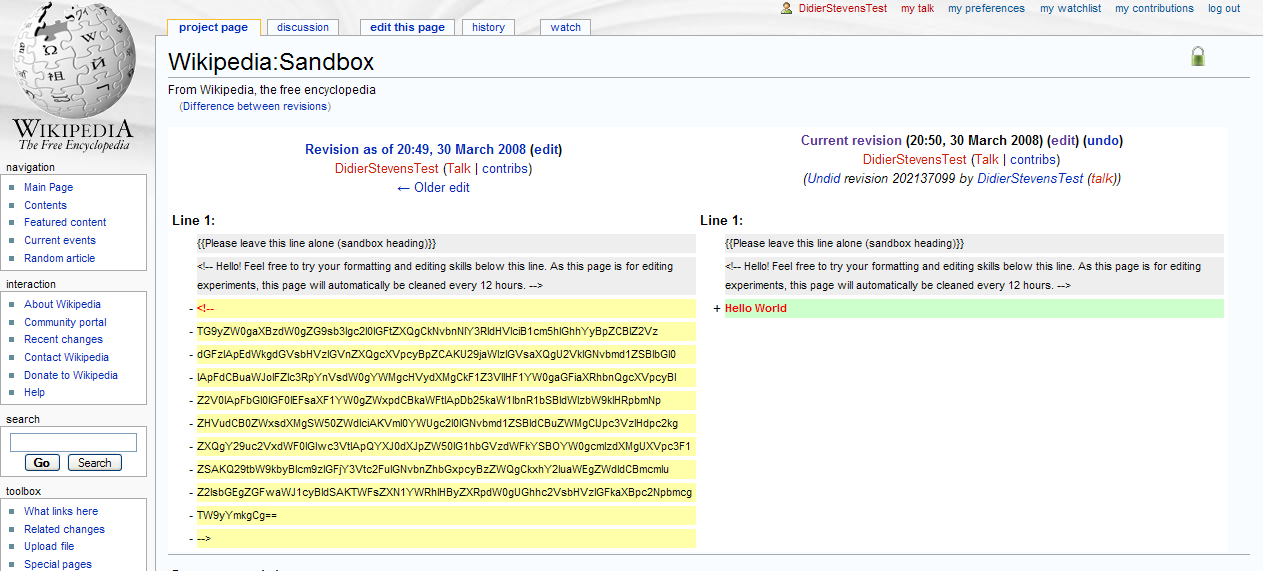
Save your changes first, and then undo your changes via the history tab:
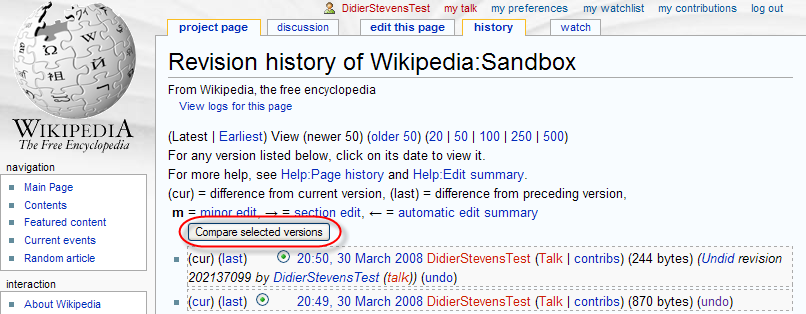
That’s it! From now on, you can retrieve your data by comparing versions:
So how can you detect and prevent this? Head over to the PaulDotCom Community Blog for the answer, where I’m a guest blogger.
[…] . You gave me a lot of ideas that will require even more time to develop. Like past years, I got a new stego idea but this time, I’m reserving it for Brucon’s hacker challenge. You’ll have to […]
Pingback by Quickpost: Black Hat Europe 2009 « Didier Stevens — Monday 27 April 2009 @ 5:47
Clever, though there are literally millions of other places you could hide information like this. Comments on abandoned blogs would be one example.
Comment by Milan — Wednesday 15 July 2009 @ 2:02
@Milan Yes, but the difference with a Wiki is that you can undo your changes. Thus your data is not in the page, but in the history of the page.
Comment by Didier Stevens — Wednesday 15 July 2009 @ 6:18
[…] OK, you can decide to block Pastebin.com. But can you block all sites that can be posted to? Like Wikipedia? And if you can, do you block ICMP […]
Pingback by PDF Info Stealer PoC « Didier Stevens — Monday 8 March 2010 @ 0:01