This update brings an update to plugin plugin_vba_dco.py.
This is a plugin that scans VBA source code for keywords (Declare, CreateObject, GetObject, CallByName and Shell), extracts all lines with these keywords, followed by all lines with identifiers associated with these keywords.
For example, if the result of a CreateObject call is stored in variable oXML, then all lines with this oXML identifier are selected.
I updated this plugin with two options -g (–generalize) and -a (–all).
Option -g generalize will replace all identifiers (like variable & functions names) with a general name: Identifier#### where #### is a numeric counter.
I added this option to analyze a sample where almost all identifiers where completely unreadable, as they consisted solely out of characters that are between byte values 128 and 255 (e.g., non-ASCII).
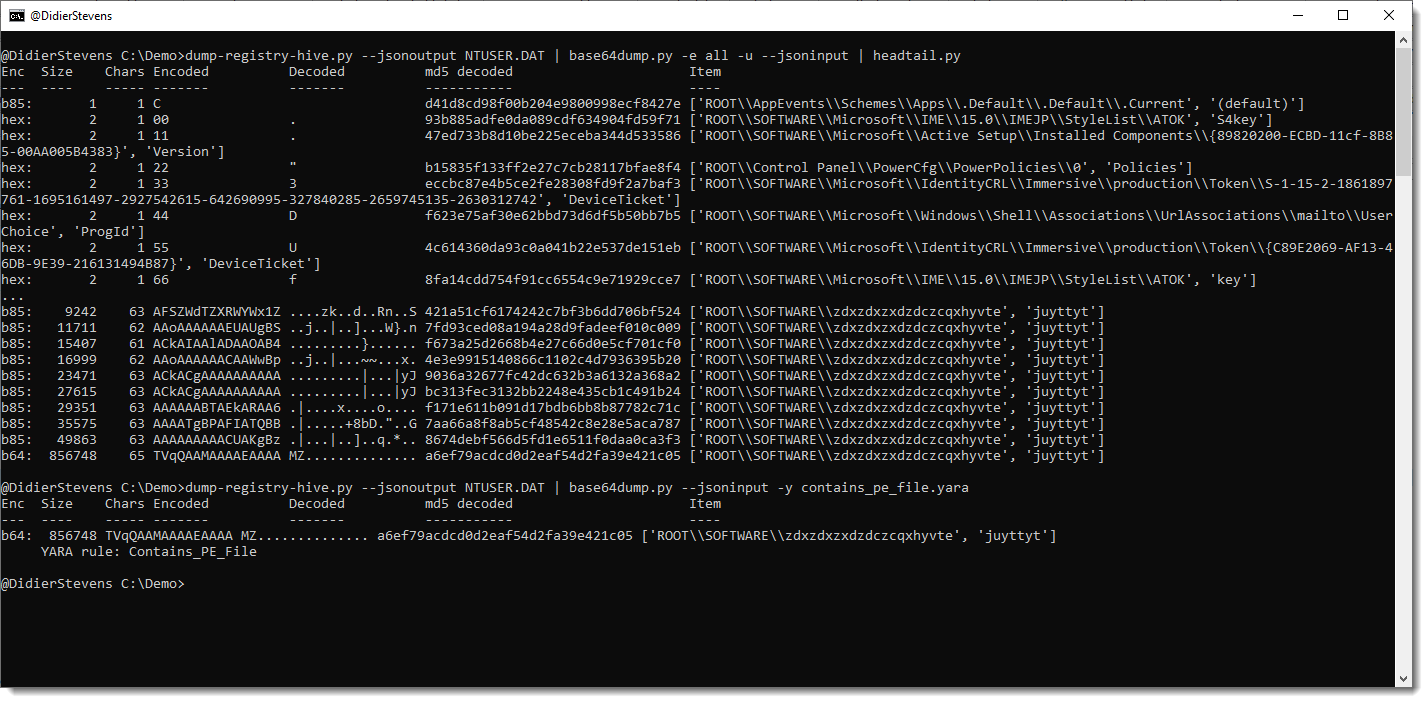
Here is the output for that sample, without using any plugin option:
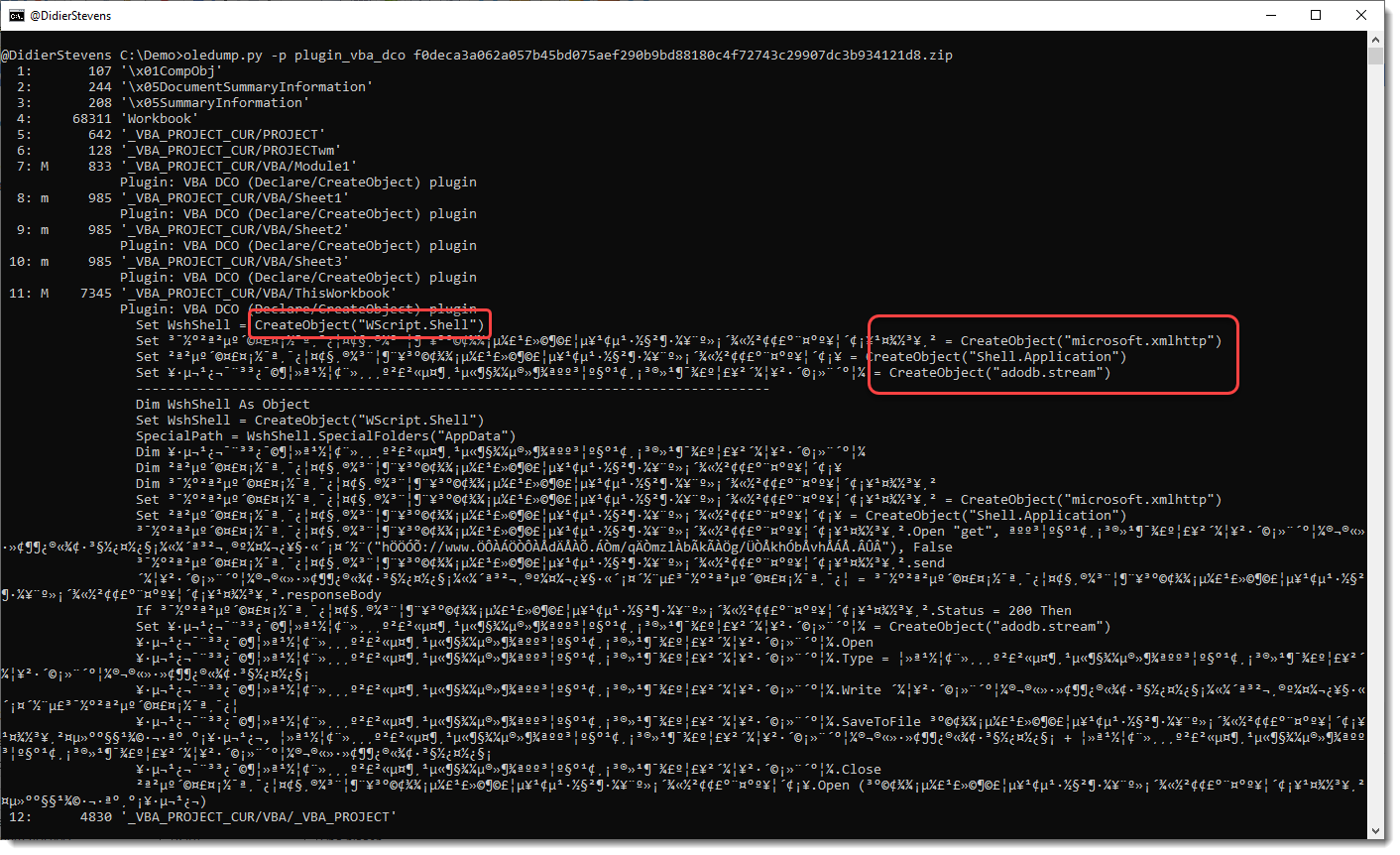
You can see the CreateObject functions, but appart from the WshShell identifier, the other identifiers don’t have letters and are hard to trace in the code.
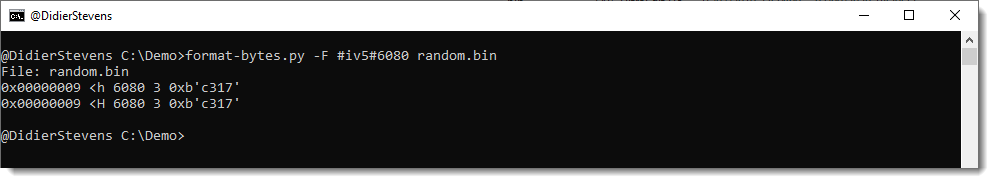
This changes when you use option -g:
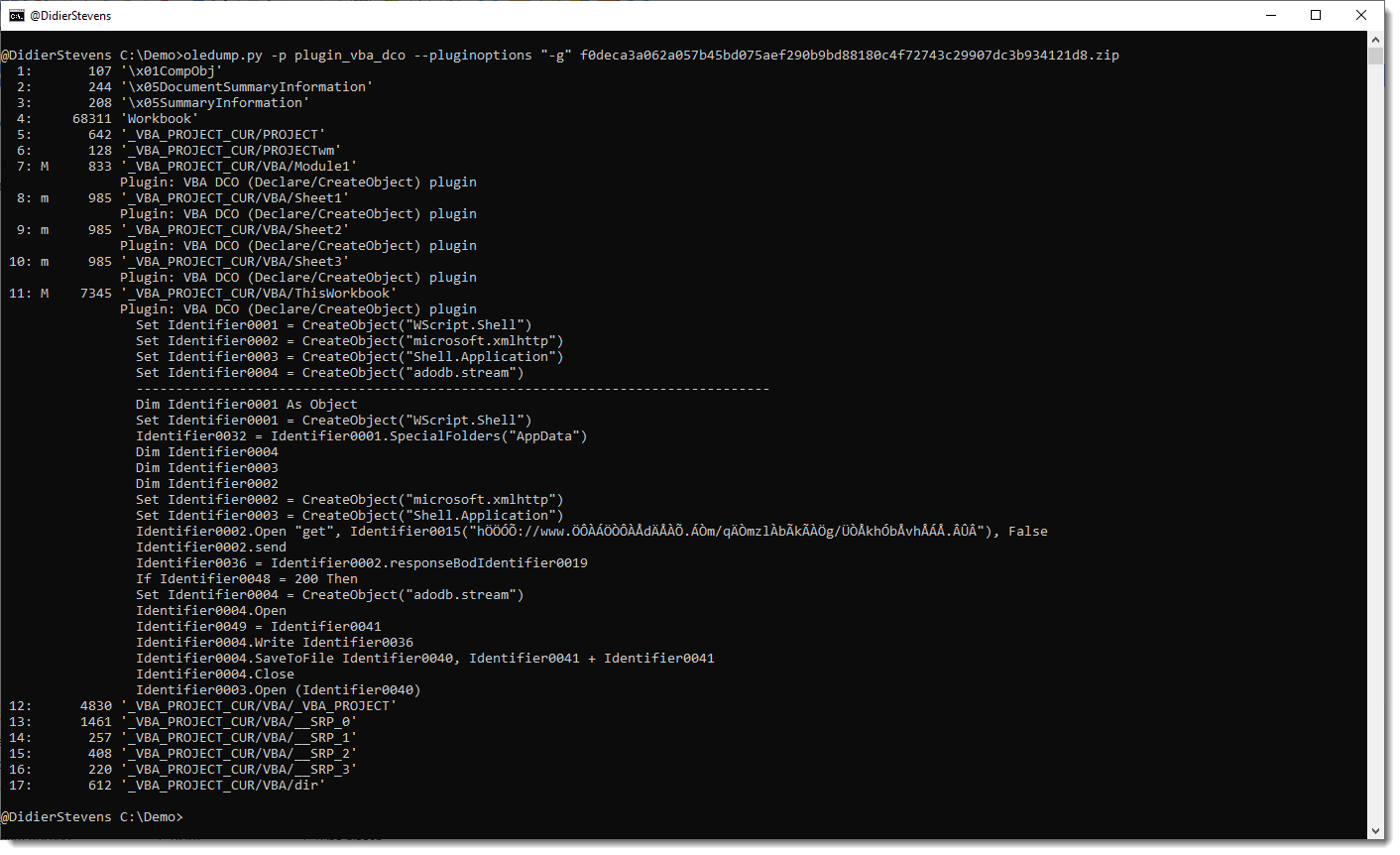
All identifiers have been generalized to names like Identifier0001, Identifier0002, …
To view all generalized code (and not only the lines with keywords), use option -a:
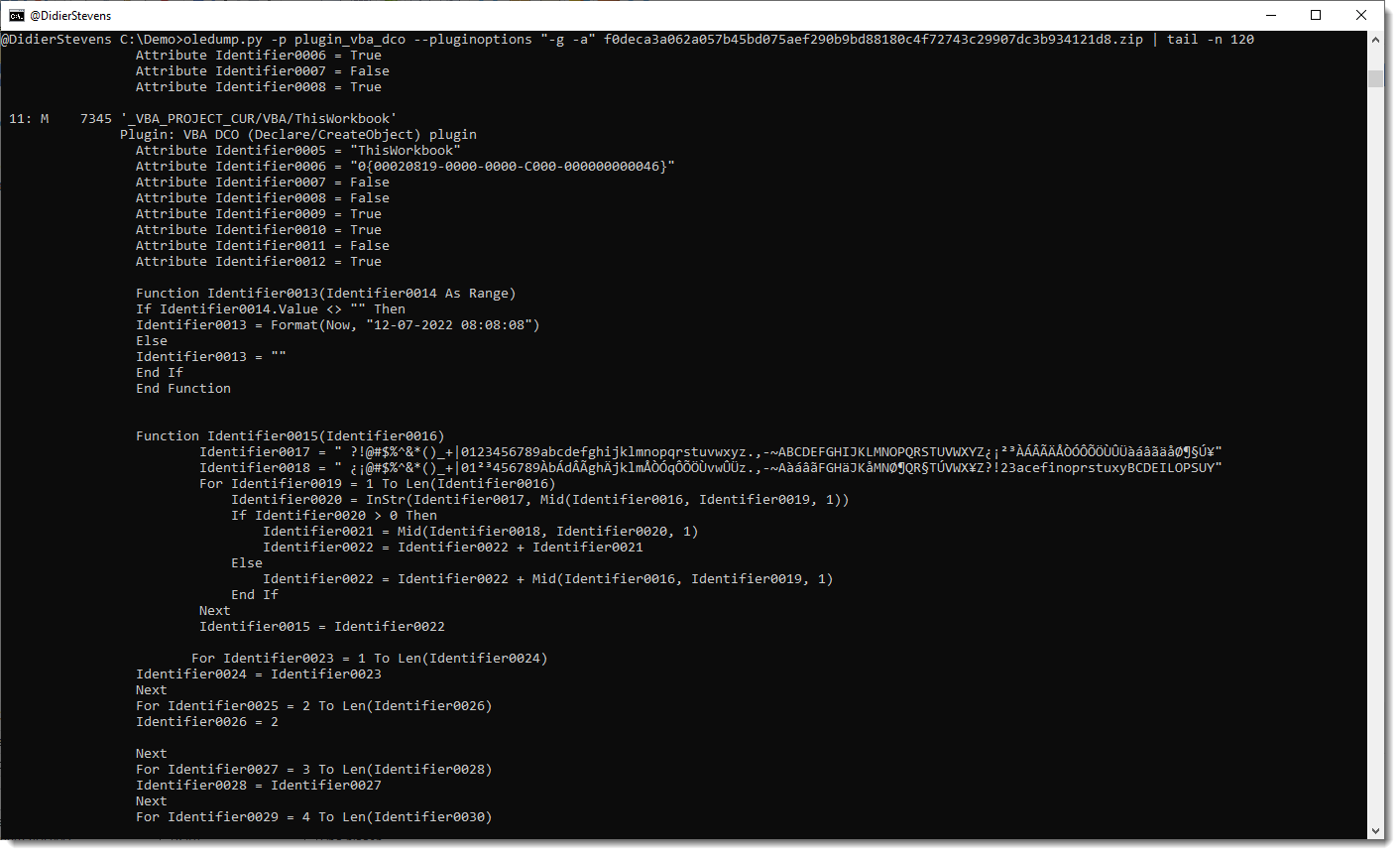
Remark that this plugin is not a VBA parser: it uses some simple scans and regexes to find identifiers. For example, it handles line comments like any other lines.
oledump_V0_0_69.zip (http)MD5: 9FDE05EB0B475C5BB76A92A926DBE8CD
SHA256: 16761C633DEC83CB691AE7223BB5AE82E5EC668F5D161499800638BC45420285