This is a fix for option –yarastrings.
base64dump_V0_0_29.zip (http)MD5: CA3FD00D6AD8B6C0CD091526E3D45D72
SHA256: 2B203BF336D4D7971E4277CE9438D271E9F002E75A2386B97BA61C543D712964
This is a fix for option –yarastrings.
base64dump_V0_0_29.zip (http)This is a fix for option –yarastrings.
rtfdump_V0_0_15.zip (http)This update adds option -C (–combinations). When this option is used together with -j (–jsonoutput), 2 extra versions of each stream are added. One with option -H enabled, and one with option -H and -S enabled.
rtfdump_V0_0_14.zip (http)This update adds pseudo-field sha256 which can be used to calculate the sha256 hash of the content (compressed or decompressed):
-E sha256:data
-E sha256:data:decompress
-E sha256:decompress
-E sha256:extra
This is a bug fix version.
hash_V0_0_14.zip (http)The Dutch government is telling people to prepare to be self-sufficient for at least 72 hours in case of a major emergency when many services (electricity, water, internet) could be unavailable. This campaign is called “Denk Vooruit” (Think Ahead). An emergency booklet has been mailed to all inhabitants. The Belgian authorities are voicing similar concerns, but no emergency booklet has been mailed.
The booklet advises people to have a radio in their emergency kit, specifically one that works without mains power, like a battery-powered or hand-crank radio.
I have a battery-powered FM radio, and I wanted to know if I could power it with a USB powerbank and a USB trigger board (I have several high-capacity powerbanks).
It works: the radio has a 12V barrel jack connector, and I can power it with this USB trigger board/cable, without soldering connectors:

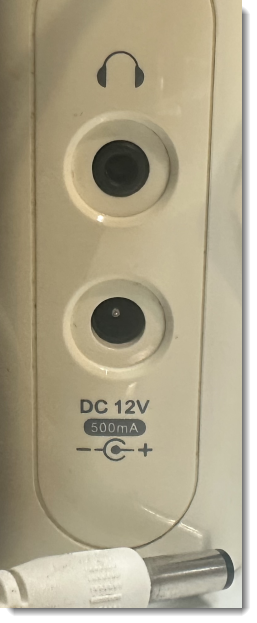

I’ll probably still solder a cable with a fixed 12V USB trigger board, because this setup is prone to accidentally pushing the button of the USB trigger board, and delivering 15V or 20V to the radio (a voltage that is too high, and might destroy the radio).
Although this setup is portable, it’s not very handy to carry around when you go away from home. So I looked around on Aliexpress for a small & cheap FM radio and selected a Junus J-555. It can be powered by two alkaline AAA batteries or by its built-in Li-Po battery. That Li-Po battery can be charged via a USB-C connector, and the radio also works while charging. But what is most important: it has a good reception of FM and AM stations when operating inside my home.