Several of my tools, that accept more than one filename as arguments, also accept a “here file” (cfr. here documents). A here file is a text file with a list of filenames, one per line. My tools recognize a here file by prefixing the filename of the here file with character @.
Let’s take for example a text file with filename list.txt and following content:
sample-1.bin sample-5.bin sample-7.bin
When using this file (list.txt) in the following command:
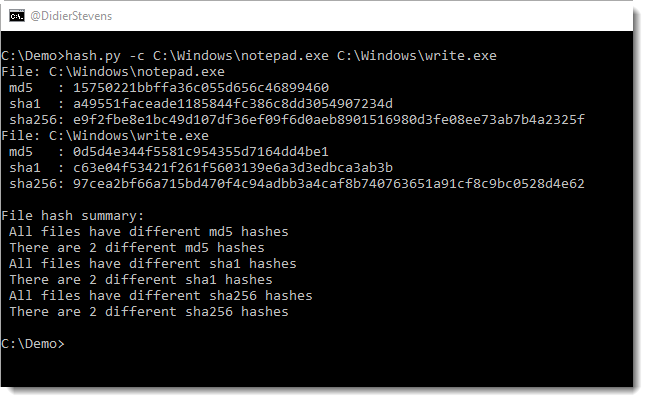
hash.py @list.txt
hash.py will calculate the hashes of the following files: sample-1.bin, sample-5.bin and sample-7.bin.
A here file can also be provided via stdin. Just type character @ (without filename) as argument to hash.py and provide a list of files via stdin, like in this example:

I will explain this any many more features of my tools in a workshop at BruCON. During this workshop, I will provide the templates I use to create my tools.
This is BruCON’s 10th edition, and I’m happy I’ll do my 10th workshop for this anniversary edition.
hash_V0_0_4.zip (https)
MD5: 6DAC25432338BEA40B9141A791B8A958
SHA256: D66BF64B91B1BCBA5EA99EA03439A12835C5427BB1C447E6B515F94D9F468137