I added support for label * (wildcard label).
dnsresolver_V0_0_3.zip (http)MD5: 18958CEEB8CD62B50D6533A477008649
SHA256: E8BB634C9D5562D640D23AA426948D166977193931794E67761F1BCD2436466E
I added support for label * (wildcard label).
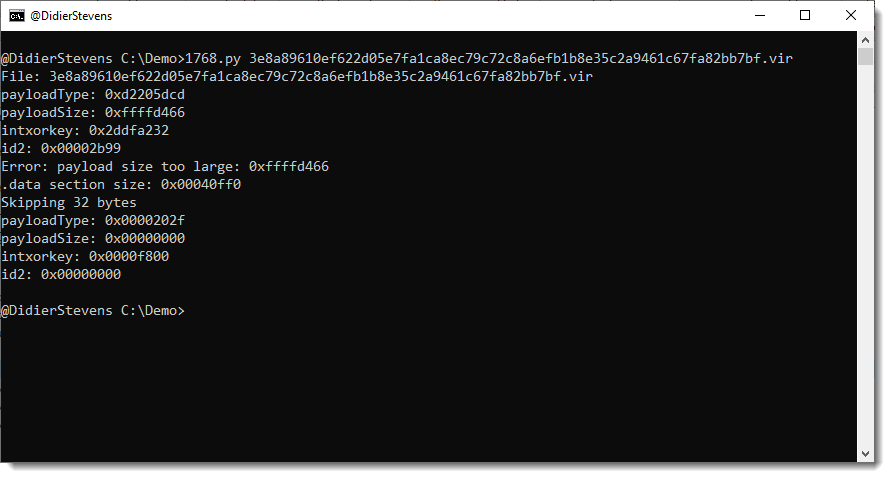
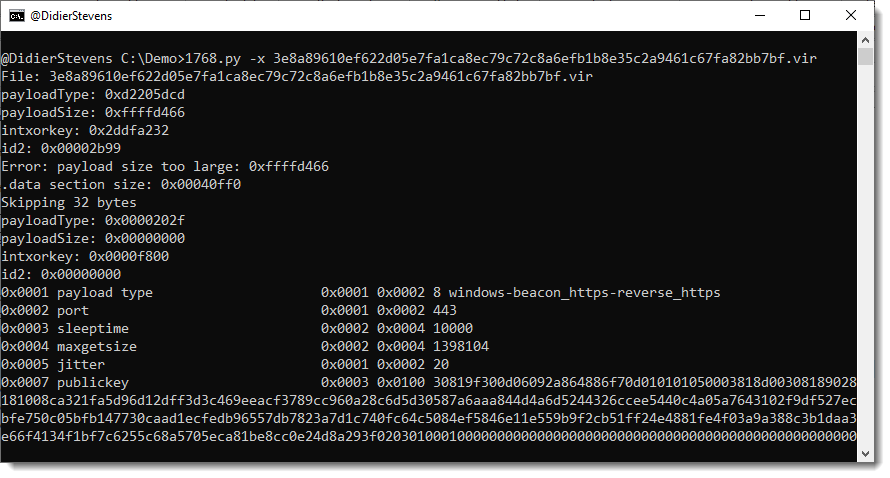
dnsresolver_V0_0_3.zip (http)This new version of 1768.py brings an option to try out all 256 xor keys if a non-standard XOR key is used to encode the configuration.
Like this sample (key !):

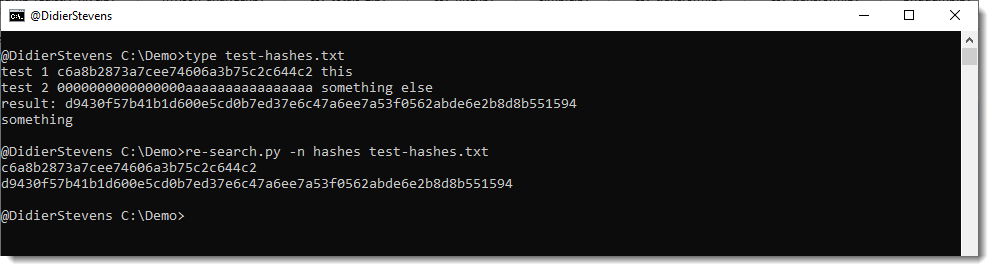
This update to re-search.py, my tool to search text files with regular expressions, brings several new regular expressions.
There are 4 new regular expressions for cryptographic hashes: md5, sha1, sha256, sha512. And one new name that groups these 4 regular expressions: hashes.
You can use it like this: re-search.py -n hashes sample.txt
These regular expressions not only match strings of hexadecimal characters of the appropriate length (with a boundary: \b), they also check each extracted hash with a Python function (HashValidate in re-extra.py) that is designed to eliminate strings that accidentally look like a hash (example: 32 times letter A).
HashValidate checks the following:
These simple rules are designed to detect hexadecimal strings that are too uniform, and thus probably not a hash digest.
And I also added regular expressions for strings delimited by single quotes: str-s, str-se str-su, str-seu.
re-search_V0_0_22.zip (http)A small update to plugin_msi_info to change the output format a bit. And you can select your preferred hash algorithm with environment variable DSS_DEFAULT_HASH_ALGORITHMS.
oledump_V0_0_74.zip (http)In this update, I add option -W to write items to disk.
Option -W takes a value. Possible values are: vir, hash, hashvir and idvir.
This value determines the filename for each item written to disk.
vir: filename is item name + extension vir
hash: filename is sha256 hash
hashvir: filename is sha256 hash + extension vir
idvir: filename is item id + extension vir
For an example, take a look at my SANS ISC diary entry “Extracting Multiple Streams From OLE Files“.
myjson-filter_V0_0_4.zip (http)This is an update to python-per-line.py, my tool to execute a Python expression one each line of a text file.
New options are –regex –join –split. And there are new string reversal functions: Reverse and ReverseFind.
More details in the man page.

A small update to plugin_msi_info to provide extra info on streams.

Indicator ! marks PE and CAB files.
Indicator ? marks files that are not images (and are not marked with !).
The idea is to first inspect streams marked with ! and ?.
The plugin also provides an overview of the files contained inside the CAB file.
oledump_V0_0_73.zip (http)This update brings a new plugin to analyze MSI files: plugin_msi_info

This is a bug fix update.
python-templates_V0_0_10.zip (http)In this new version of cut-bytes.py, I add support for custom Python transforms (options -P and -S), pyzipper and fixed a bug.
cut-bytes_V0_0_16.zip (http)