This new version of re-search.py adds a regex for UNCs to the library and has a Python 3 fix.

MD5: 294DD5D4027F0AFD0A2DE6432FE4552D
SHA256: B818CE4F7E217B381128550A3A36B40B6D07CC687CE4CF5AFF3C70EC0D3EEAD2
This new version of re-search.py adds a regex for UNCs to the library and has a Python 3 fix.

This update brings an update to plugin plugin_vba_dco.py.
This is a plugin that scans VBA source code for keywords (Declare, CreateObject, GetObject, CallByName and Shell), extracts all lines with these keywords, followed by all lines with identifiers associated with these keywords.
For example, if the result of a CreateObject call is stored in variable oXML, then all lines with this oXML identifier are selected.
I updated this plugin with two options -g (–generalize) and -a (–all).
Option -g generalize will replace all identifiers (like variable & functions names) with a general name: Identifier#### where #### is a numeric counter.
I added this option to analyze a sample where almost all identifiers where completely unreadable, as they consisted solely out of characters that are between byte values 128 and 255 (e.g., non-ASCII).
Here is the output for that sample, without using any plugin option:
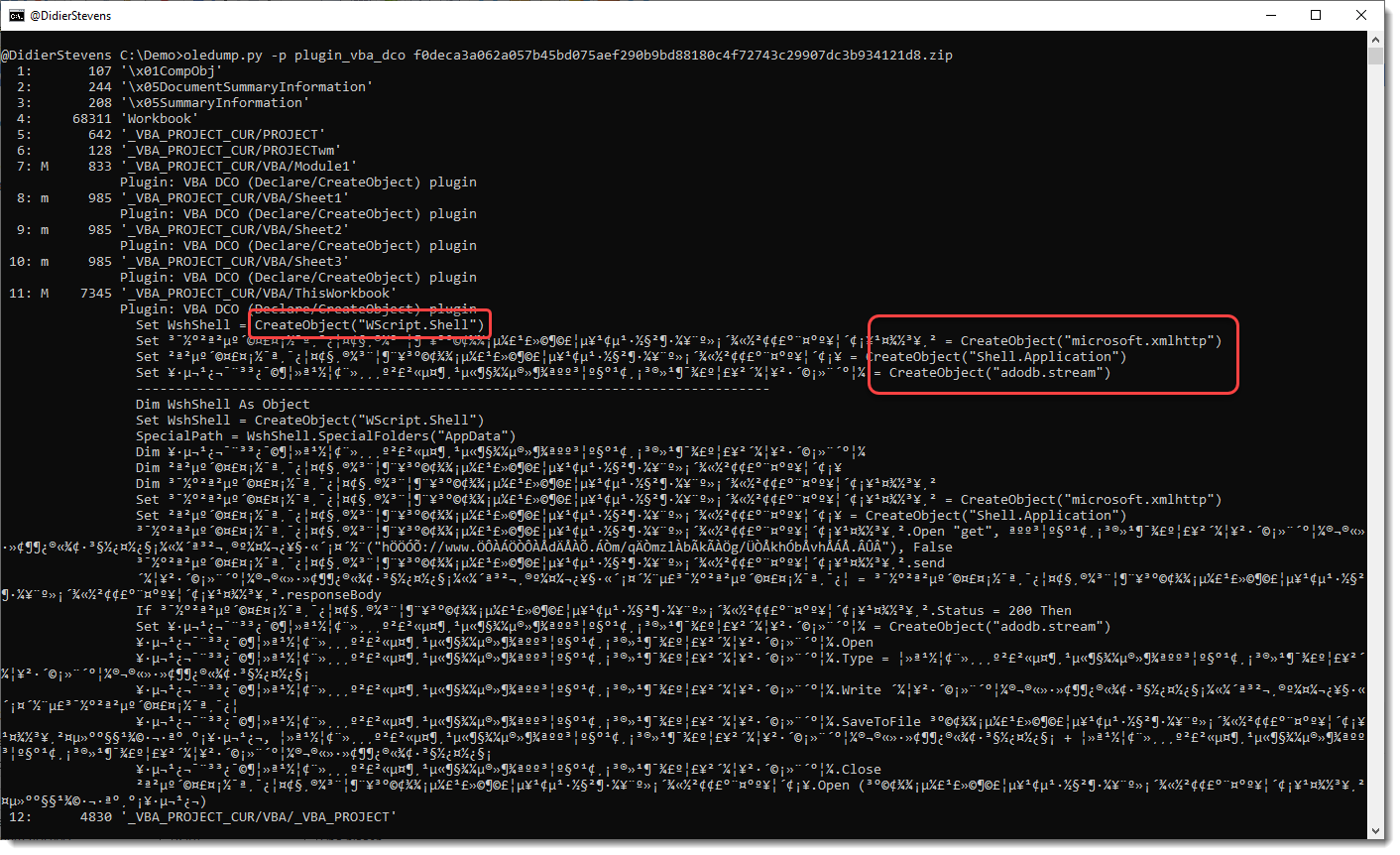
You can see the CreateObject functions, but appart from the WshShell identifier, the other identifiers don’t have letters and are hard to trace in the code.
This changes when you use option -g:
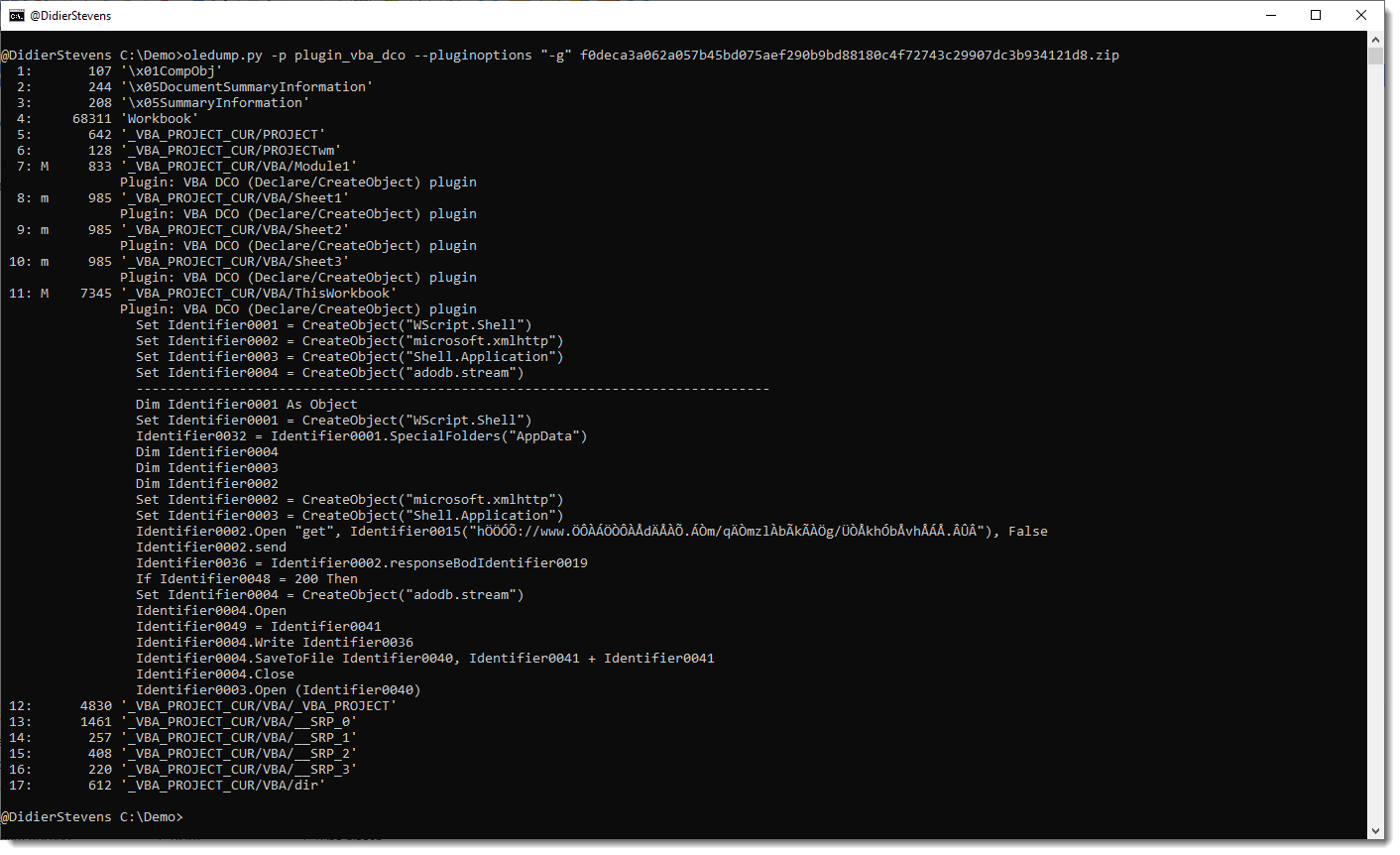
All identifiers have been generalized to names like Identifier0001, Identifier0002, …
To view all generalized code (and not only the lines with keywords), use option -a:
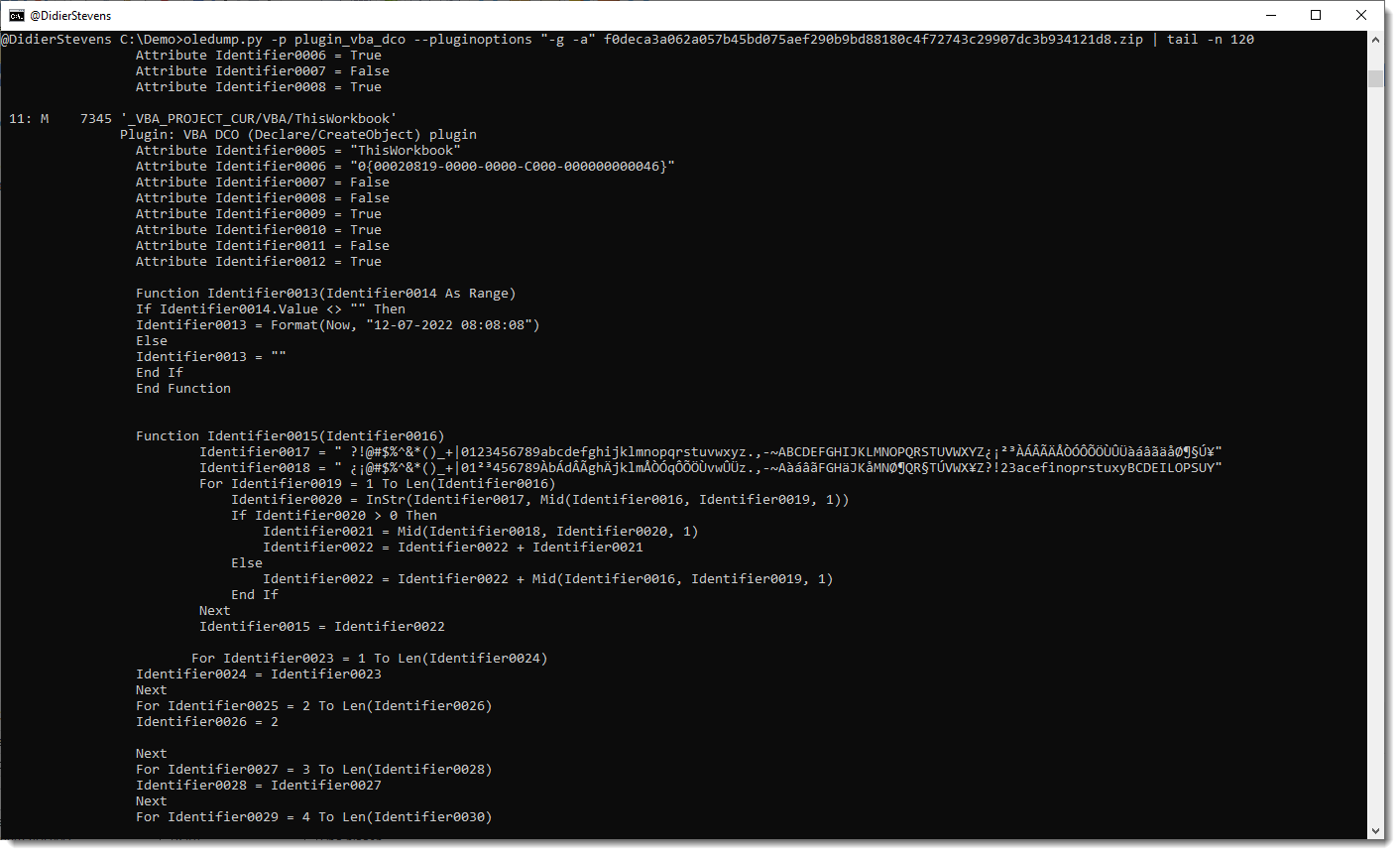
Remark that this plugin is not a VBA parser: it uses some simple scans and regexes to find identifiers. For example, it handles line comments like any other lines.
oledump_V0_0_69.zip (http)This new version adds a sort function to sort email addresses by domain first.
sortcanon_V0_0_2.zip (http)This new version adds JSON input support, allowing,for example, to detect encoded payloads inside the registry:
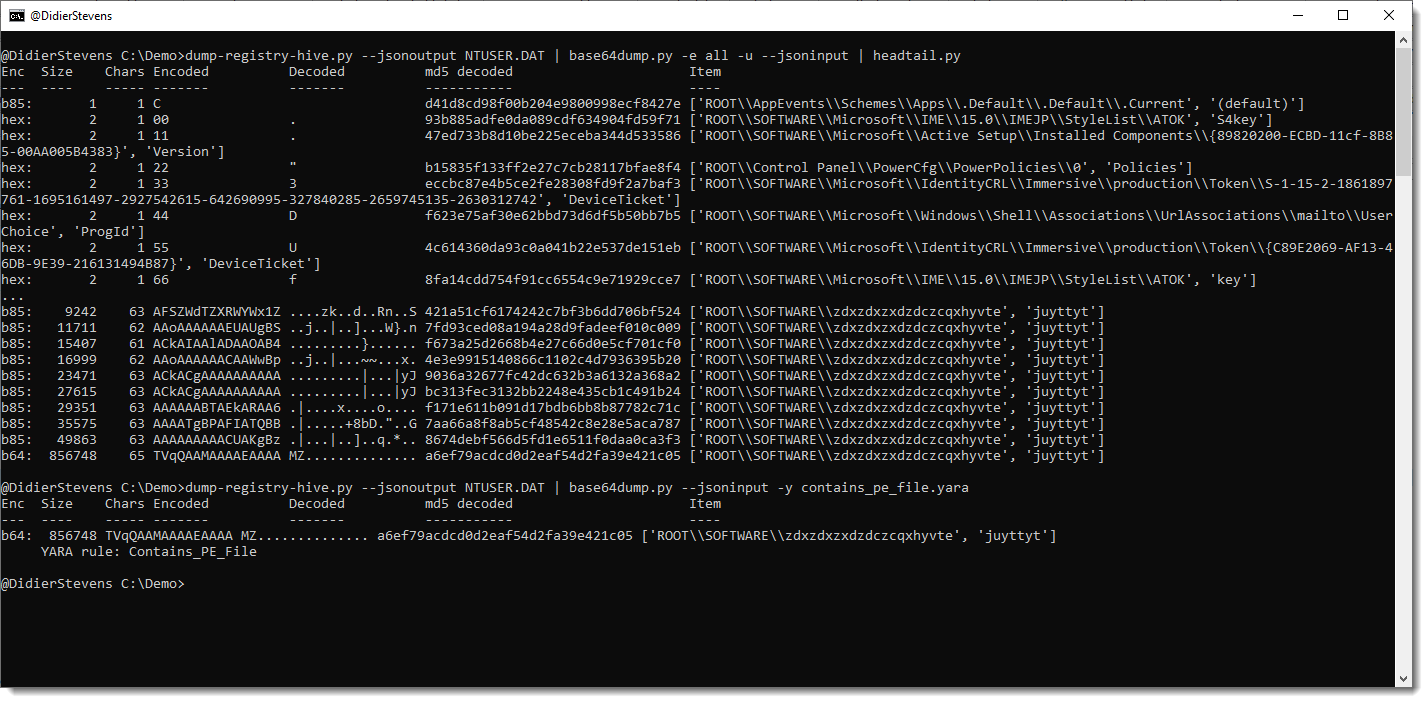
More info in an upcoming blog post.
base64dump_V0_0_23.zip (http)I did some tests with my USB chargers: how much power do they consume when plugged into a power socket without charging any device (standby)?
The devices I tested are:
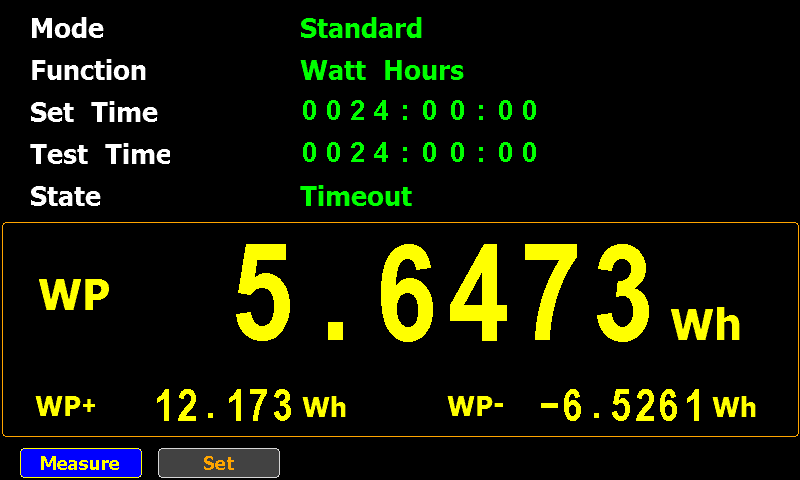
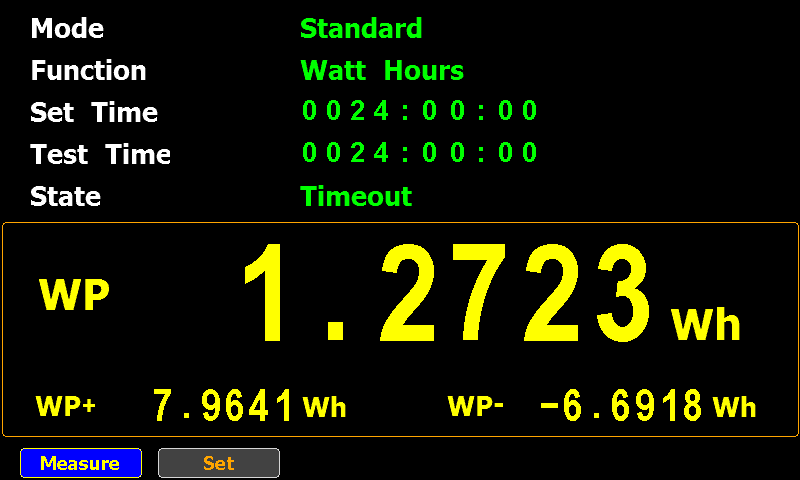
I connected each one to a powermeter and let it measure the standby power consumption for 24 hours.
This is the result:
| Model | 24 hours (Wh) | 1 hour (Wh) | 1 year (Wh) |
| Apple A1357 | 2,8847 | 0,1202 | 1052,9155 |
| Apple A2347 | 1,2723 | 0,0530 | 464,3895 |
| Anker A2053 | 5,0734 | 0,2114 | 1851,7910 |
| No-brand: Chacon EMP604USB | 5,6473 | 0,2353 | 2061,2645 |
24 hours is the measured data, the “1 hour” and “1 year” columns are calculated based on the 24 hours data.
The no-brand USB charger consumes the most: around 2 kWh per year, which is still less than a switched off Philips Hue lamp.
Using the same cost as for the Philips Hue lamp, that no-brand charger costs me around €1 if I would leave it plugged in for a whole year without letting it charge anything.



This is the release of simple_listener.py, a Python program that can accept TCP and UDP connections and react according to its configuration. It has evolved from my beta program tcp-honeypot.py, that I will no longer maintain.
Everything you could do with tcp-honeypot, can be done with simple_listener.
I use simple_listener now whenever I need a server that listens for incoming TCP and/or UDP connections. For example, I have a configuration that can accept connections from Cobalt Strike beacons using leaked private keys.
simple_listener has a full man page, explaining all configuration items and options.
simple_listener_v0_1_2.zip (http)This new version of format-bytes.py adds a feature to search for a range of integers:
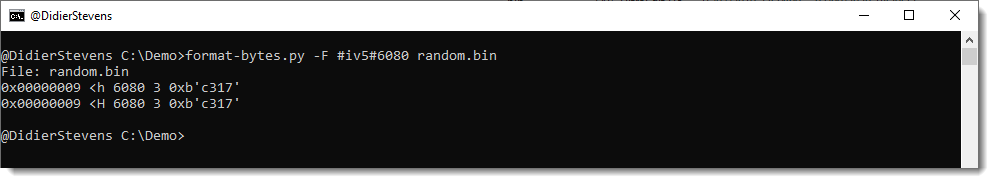
#iv5#6080 means: look for an integer (i) equal to 6080 with a variation of 5 (v5), e.g., look for integers between 6075 and 6085.
format-bytes_V0_0_14.zip (http)This new version contains a Python 3 fix.
cut-bytes_V0_0_15.zip (http)I added code to John the Ripper to crack PDF owner passwords (JtR cracks PDF user passwords only).
Source code can be found here.
Compiled Windows (Cygwin) and Linux (Ubuntu) executables can be found here.
This change introduces a new format: $pdfo$.
There is no tool for the moment to create this format. Just use pdf2john.pl to create a $pdf$ hash, and then change it into a $pdfo$ hash. To crack the owner password, one needs to recover the user password first.
This is the illustrated process:

There will be a PR for this change.
Cracking PDF owner passwords is just an academic exercise (writing this code was also just an exercise), as tools like QPDF can decrypt PDFs encrypted with a PDF owner password only without requiring the cleartext PDF owner password as argument.