The title of this post is inspired by Mark Russinovich‘s posts. I explain why there is a category of executables with a digital signature that don’t show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures.
Executables (PE files) can have a digital signature, Microsoft calls this signature AuthentiCode. There are 2 different ways to sign a PE file: by adding a digital signature to the PE file (embedded digital signature) or by adding a hash of the PE file to a security catalog file (filetype .CAT).
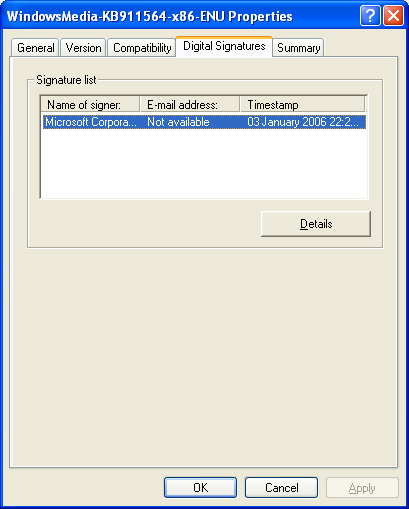
The Properties dialog of a file hosts a Digital Signatures tab when the PE file has an embedded digital signature, like this Windows patch from Microsoft:
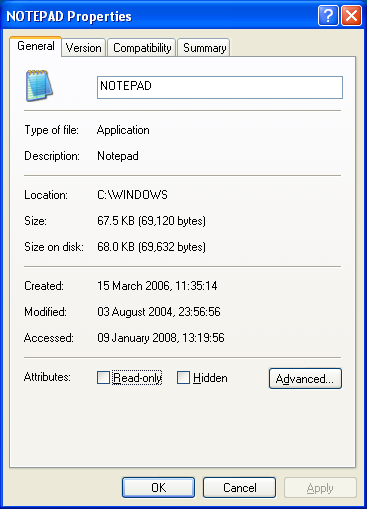
But when a file is signed via a security catalog file, the Digital Signatures tab is not displayed. Notepad is a good example:
To check the digital signature of this category of files, one uses Microsoft’s signtool or Mark’s sigcheck utility:
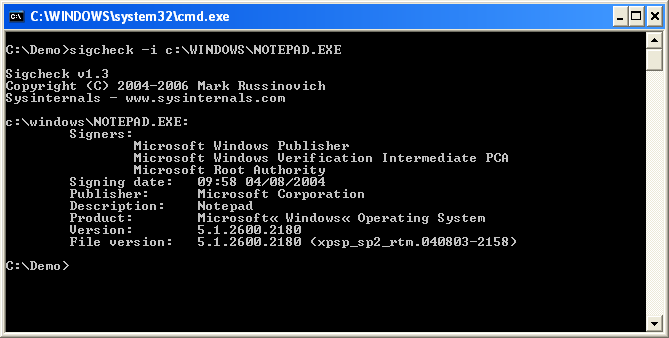
These tools will calculate the hash of the file, look it up in the appropriate security catalog file and check the signature of the security catalog file. One can find security catalog files in directory C:\windows\system32\catroot:
For an embedded digital signature, the location of the signature is at the end of the signed file. Look for DATA_DIR Security in IMAGE_DATA_DIRECTORIES of the optional PE header. It has a pointer (4 bytes) to the signature and the length (4 bytes) of the signature. The pointer is just the offset in the binary file. When these bytes are all zero (0x00), the PE file has no embedded digital signature.
Here is the PE header of another Windows patch:
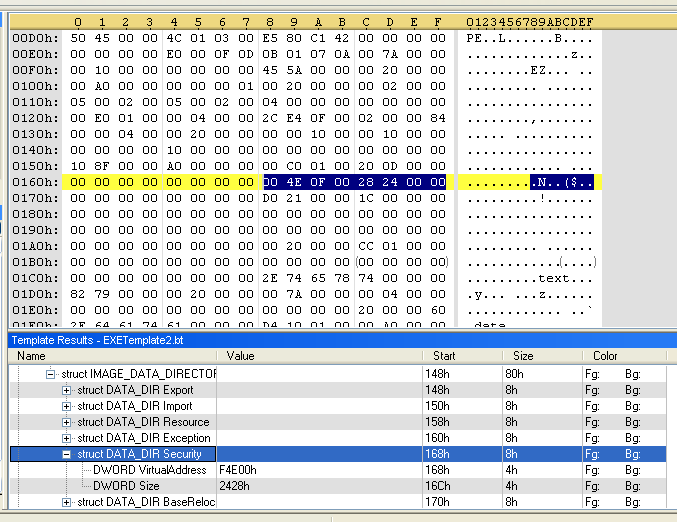
In this patch, the signature entry can be found at offset 0xF4E00 in the file and is 0x2428 bytes long:
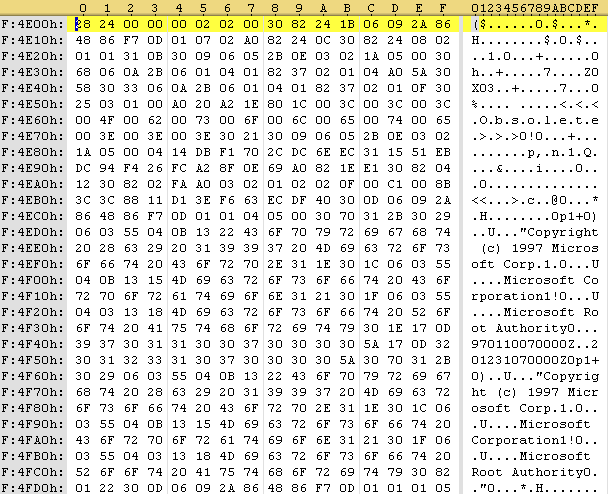
The first 4 bytes of the signature entry is the size, the following 4 bytes is a constant (0x00020200), and the rest is the PKCS7 signature. This signature can be extracted with a binary editor and parsed with openssl:

Finally, I wrote a small Python program to manipulate embedded digital signatures. Features of disitool:
- delete a signature: disitool.py delete signed-file unsigned-file
- copy a signature: disitool.py copy signed-source-file unsigned-file signed-file
- extract a signature: disitool.py extract signed-file signature
- add a signature: disitool.py add signature unsigned-file signed-file
This was very interesting. I have one question and maybe its because I didn’t quite understand much about digital signatures. But could a hacker somehow use those hidden digital signatures to put something malicious on your system?
BTW, I check your blog almost daily.
There is one thing that I would really appreciate. Could you display an excerpt on the main page of your blog so I don’t have to go through an entire post just to find out if I missed something (skipped a day because I wasn’t at my computer or maybe you had two posts in a particular day).
Also, it might be easier to read the text on your images if you’d reduce them to the width of your blog post. For me the images are overlapping the text on the right side.
Thanks for such a good blog.
Comment by Charlene — Friday 11 January 2008 @ 16:11
The Wikipedia link about Code Signing at the beginning of the post gives an excellent intro about digital signing code:
Code signing is the process of digitally signing executables and scripts to confirm the software author and guarantee that the code has not been altered or corrupted since it was signed by use of a checksum.
The only way I can see that a malware author could use digital signatures to execute code on your system, is when he finds a vulnerability in the code that deals with signatures, and finds en exploit to execute remotely. But then he would also have to social engineer you into checking the digital signature, because I don’t think the signature is parsed automatically.
There are only 2 vulnerabilities that I see related to AuthentiCode. There was one that allowed the bypass of the AuthentiCode check in IE, and there was one in the ASN1 parsing.
I don’t have much flexibility with the layout of my blog, as I don’t host my own WordPress software on my own server. This blog is hosted by WordPress.com
Comment by Didier Stevens — Wednesday 16 January 2008 @ 20:39
[…] and MD5 Collisions Filed under: Encryption, Hacking — Didier Stevens @ 15:11 Back when I researched Microsoft’s code signing mechanism (Authenticode), I noticed it still supported MD5, but that the signtool uses SHA1 by […]
Pingback by Playing With Authenticode and MD5 Collisions « Didier Stevens — Saturday 17 January 2009 @ 15:12
Thank you very much, I’ve been trying to understand where the heck the signatures went!
Comment by egilam — Thursday 22 January 2009 @ 13:11
[…] I found another file in this _restore folder: A0000615.cat. This is a catalog file that Microsoft uses to sign Windows executables. With Sysinternals’ sigcheck tool and this catalog file, I was able to confirm that this is a […]
Pingback by Forensic Use of CAT Files | Didier Stevens — Monday 3 March 2014 @ 0:17
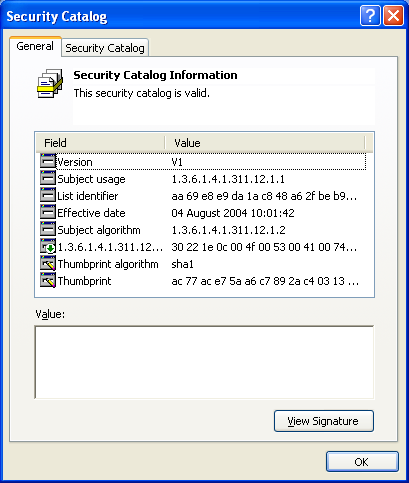
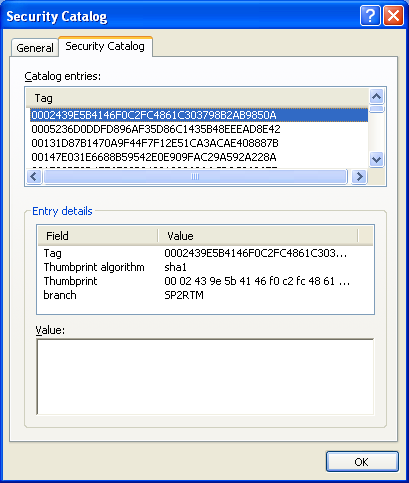
The fourth image of this tutorial shows the hash content of a driver security catalog.
How to show the content of a driver .cat file ?
Thanks
Comment by Mark — Monday 9 January 2017 @ 11:39
It’s in the 5th image.
Comment by Didier Stevens — Monday 9 January 2017 @ 20:01
… sorry, It’s in the 5th image, but the image example seems to suggest to right click on a .cat file and choose the properties option to show the tabs of the pic, but this is not working on Windows 7 Pro, Windows XP Pro sp3 and Windows 8.1 even for files inside C:\windows\system32\catroot\ directory.
Comment by Mark — Tuesday 10 January 2017 @ 14:56
No, not right-click, but double-click.
Comment by Didier Stevens — Tuesday 10 January 2017 @ 17:43
Hello. Is there a way to extract the signed certificate inside the exe in command line mode (not python version)?
Because you forgot to show how to get patch.der to analyze with openssl to show the header.
Where did you get that file?
Comment by milo8080 — Tuesday 5 February 2019 @ 0:01
Hi. No, I didn’t forget it. Maybe you missed it, but I explain it in my blog post:
> The first 4 bytes of the signature entry is the size, the following 4 bytes is a constant (0x00020200), and the rest is the PKCS7 signature.
Comment by Didier Stevens — Tuesday 5 February 2019 @ 0:41
[…] this article (linked by JosefZ) says, the Digital Signatures tab only appears if the signature is in the file […]
Pingback by Windows Explorer file property does NOT show digital signature info for some system file, why? - Boot Panic — Sunday 31 October 2021 @ 12:55