When I found a malicious script riddled with 0x00 bytes, SANS handler Bojan Zdrnja explained to me that this was an old trick. When rendering an HTML page, Internet Explorer will ignore all zero-bytes (bytes with value zero, 0x00). Malware authors use this to obscure their scripts. But this old trick still packs a punch.
This is how the script looks in vi:

Maybe this hex dump makes it more clear to you:
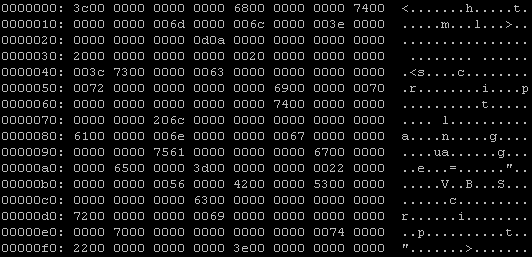
Recognize <html> <script…?
Well, a lot of AV programs are still fooled by this trick, VirusTotal reports that only 15 out of 32 AV products detect this malicious script.

When I remove all obscuring zero-bytes from this script, things get better: 25 out of 32 AV products detect it.
But what happens when I add more zero-bytes to the script?
Even more AV are fooled! Gradually adding more zero-bytes makes the detection ratio go down.
And at 254 zero-bytes between the individual characters of the script, McAfee VirusScan is the only AV to still detect this obscured script. One byte more (255 zero-bytes), and VirusScan doesn’t detect the script anymore. No AV on VirusTotal detects this malware obscured with 255 zero-bytes (or more). But for IE, this obscured HTML poses no problem, it still renders the page and executes the script.
But you cannot rely on VirusTotal results alone. Modern AV products do not solely rely on file scanning to identify malware, they come with many techniques. For example, VirusScan has a feature called ScriptScan, a utility that intercepts all script execution requests to the MS scripting engines (VBS & JS). Since IE sends the malicious script stripped of its zero-bytes to the VBS scripting engine, ScriptScan has no problem detecting the malware and prevents its execution.
As it is the first time I get such a clear example of ScriptScan in action, I’ve made a screencast (YouTube) of it, XviD hires here.
How does firefox handle zero bytes? Do they all treat them as IE does?
Comment by DF — Tuesday 23 October 2007 @ 15:33
FF will ignore 1 zero byte, like ASCII code represented in Unicode. 2 zero bytes and the page is not rendered correctly.
Don’t know about other browsers.
Comment by Didier Stevens — Tuesday 23 October 2007 @ 15:50
[…] When Didier Stevens recently took a closer look at some Internet Explorer malware that he had found, something surprised him somwehat. He discovered that the IE-targeted malware had been obfuscated […]
Pingback by Anti-virus products fail simple malware test « Technology Info — Monday 29 October 2007 @ 19:27
I’m not seeing a result for Kaspersky, the best antivirus out of all which exists today… though maybe you might not read white papers and other sites like http://www.virus.gr *wink*
Where does Kaspersky stand up in your tests?
Comment by David Ross — Monday 29 October 2007 @ 19:51
Here are the complete VirusTotal results for the original malware, followed by the results for the stripped malware:
File 02.hker.htm received on 10.09.2007 15:15:48 (CET)
Current status: Loading … queued waiting scanning finished NOT FOUND STOPPED
Result: 15/32 (46.88%)
Loading server information…
Your file is queued in position: 2.
Estimated start time is between 43 and 62 seconds.
Do not close the window until scan is complete.
The scanner that was processing your file is stopped at this moment, we are going to wait a few seconds to try to recover your result.
If you are waiting for more than five minutes you have to resend your file.
Your file is being scanned by VirusTotal in this moment,
results will be shown as they’re generated.
Compact Compact
Print results Print results
Your file has expired or does not exists.
Service is stopped in this moments, your file is waiting to be scanned (position: ) for an undefined time.
You can wait for web response (automatic reload) or type your email in the form below and click “request” so the system sends you a notification when the scan is finished.
Email:
Antivirus Version Last Update Result
AhnLab-V3 2007.10.9.1 2007.10.09 HTML/Adodb
AntiVir 7.6.0.20 2007.10.09 TR/Dldr.Agent.DV.2
Authentium 4.93.8 2007.10.08 is a destructive program
Avast 4.7.1051.0 2007.10.08 –
AVG 7.5.0.488 2007.10.09 JS/Downloader.Agent
BitDefender 7.2 2007.10.09 Trojan.Exploit.Js.Adodb.Stream.K
CAT-QuickHeal 9.00 2007.10.08 –
ClamAV 0.91.2 2007.10.09 –
DrWeb 4.44.0.09170 2007.10.09 VBS.Psyme.239
eSafe 7.0.15.0 2007.10.08 –
eTrust-Vet 31.2.5198 2007.10.09 –
Ewido 4.0 2007.10.09 –
FileAdvisor 1 2007.10.09 –
Fortinet 3.11.0.0 2007.10.09 HTML/ObscuredHtml.TAA!exploit
F-Prot 4.3.2.48 2007.10.08 Trojan!a764
F-Secure 6.70.13030.0 2007.10.09 Trojan-Downloader.VBS.Agent.dv
Ikarus T3.1.1.12 2007.10.09 Trojan-Downloader.VBS.Agent.dv
Kaspersky 7.0.0.125 2007.10.09 Trojan-Downloader.VBS.Agent.dv
McAfee 5136 2007.10.08 Exploit-ObscuredHtml
Microsoft 1.2908 2007.10.09 –
NOD32v2 2580 2007.10.09 JS/Exploit.ADODB.Stream.Y
Norman 5.80.02 2007.10.09 –
Panda 9.0.0.4 2007.10.09 –
Prevx1 V2 2007.10.09 –
Rising 19.44.12.00 2007.10.09 Trojan.DL.VBS.Agent.p
Sophos 4.22.0 2007.10.09 –
Sunbelt 2.2.907.0 2007.10.08 –
Symantec 10 2007.10.09 –
TheHacker 6.2.6.080 2007.10.09 –
VBA32 3.12.2.4 2007.10.08 –
VirusBuster 4.3.26:9 2007.10.08 –
Webwasher-Gateway 6.0.1 2007.10.09 Trojan.Dldr.Agent.DV.2
Additional information
File size: 7456 bytes
MD5: ed949a6309c1f8bd4b0f63d422eef155
SHA1: b29356bdbf73b0b0f50212b2fcbd623743b75858
File 04.hker.htm received on 10.09.2007 15:23:53 (CET)
Current status: Loading … queued waiting scanning finished NOT FOUND STOPPED
Result: 25/32 (78.13%)
Loading server information…
Your file is queued in position: 2.
Estimated start time is between 43 and 62 seconds.
Do not close the window until scan is complete.
The scanner that was processing your file is stopped at this moment, we are going to wait a few seconds to try to recover your result.
If you are waiting for more than five minutes you have to resend your file.
Your file is being scanned by VirusTotal in this moment,
results will be shown as they’re generated.
Compact Compact
Print results Print results
Your file has expired or does not exists.
Service is stopped in this moments, your file is waiting to be scanned (position: ) for an undefined time.
You can wait for web response (automatic reload) or type your email in the form below and click “request” so the system sends you a notification when the scan is finished.
Email:
Antivirus Version Last Update Result
AhnLab-V3 2007.10.9.1 2007.10.09 HTML/Adodb
AntiVir 7.6.0.20 2007.10.09 EXP/ADODB.Stream.Y.18
Authentium 4.93.8 2007.10.08 VBS/Psyme.BT@dl
Avast 4.7.1051.0 2007.10.08 JS:Adodb-M
AVG 7.5.0.488 2007.10.09 JS/Downloader.Agent
BitDefender 7.2 2007.10.09 Trojan.Exploit.Js.Adodb.Stream.K
CAT-QuickHeal 9.00 2007.10.08 EXP_JS/ADODBStream.E
ClamAV 0.91.2 2007.10.09 –
DrWeb 4.44.0.09170 2007.10.09 VBS.Psyme.239
eSafe 7.0.15.0 2007.10.08 VBS.Phel.a
eTrust-Vet 31.2.5198 2007.10.09 VBS/Petch
Ewido 4.0 2007.10.09 Not-A-Virus.Exploit.JS.ADODB.Stream.y
FileAdvisor 1 2007.10.09 –
Fortinet 3.11.0.0 2007.10.09 VBS/AdodbStream.Y!exploit
F-Prot 4.3.2.48 2007.10.08 VBS/Psyme.BT@dl
F-Secure 6.70.13030.0 2007.10.09 VBS/Psyme.BT@dl
Ikarus T3.1.1.12 2007.10.09 Exploit.JS.ADODB.Stream.y
Kaspersky 7.0.0.125 2007.10.09 Exploit.JS.ADODB.Stream.y
McAfee 5136 2007.10.08 Exploit-MS06-014
Microsoft 1.2908 2007.10.09 TrojanDownloader:VBS/Psyme.gen
NOD32v2 2580 2007.10.09 JS/Exploit.ADODB.Stream.Y
Norman 5.80.02 2007.10.09 VBS/Psyme.AK
Panda 9.0.0.4 2007.10.09 –
Prevx1 V2 2007.10.09 –
Rising 19.44.12.00 2007.10.09 Trojan.DL.VBS.Agent.p
Sophos 4.22.0 2007.10.09 Troj/Psyme-DA
Sunbelt 2.2.907.0 2007.10.08 –
Symantec 10 2007.10.09 Downloader
TheHacker 6.2.6.080 2007.10.09 –
VBA32 3.12.2.4 2007.10.08 –
VirusBuster 4.3.26:9 2007.10.08 JS.Psyme.DO
Webwasher-Gateway 6.0.1 2007.10.09 Exploit.ADODB.Stream.Y.18
Additional information
File size: 1262 bytes
MD5: 1eb95e3f5ed72c2b19bf991b93bb7922
SHA1: 55757d42945c1dc569f7f5c97c4bc513e03feb62
Comment by Didier Stevens — Monday 29 October 2007 @ 20:10
Results from VirusTotal are not true indication of a AntiVirus program’s full capabilities since VT does a flat file scan. Try browsing to the same link using NIS/NAV2008 and Browser Defender will easily catch it.
In fact try tweaking the script some more and then you will start to see some of those 15 that detect it, suddenly stop detecting the additional obfuscation.
Comment by Symantec — Monday 29 October 2007 @ 20:36
I notice they’re using Sophos 4.22. I’m running 4.23E, on version 7.0.4. I have to wonder how the latest greatest would fare.
Comment by David Rickard — Monday 29 October 2007 @ 20:38
@Symantec
>Results from VirusTotal are not true indication of a AntiVirus program’s full capabilities since VT does a flat file scan.
Yep, that’s what I said in my blogpost, you should read it till the end:
But you cannot rely on VirusTotal results alone. Modern AV products do not solely rely on file scanning to identify malware.
> In fact try tweaking the script some more and then you will start to see some of those 15 that detect it, suddenly stop detecting the additional obfuscation.
Again, yep, that’s what I said:
But what happens when I add more zero-bytes to the script? Even more AV are fooled! Gradually adding more zero-bytes makes the detection ratio go down.
Comment by Didier Stevens — Monday 29 October 2007 @ 20:46
Why don’t place to blame IE(Microsoft) instead of antivirus companies? If it’s an old trick, Microsoft should have patched it up a long time ago. This fonts on this site hur my eyes, I’m blaming that on you, Didier Stevens.
Comment by Stan — Monday 29 October 2007 @ 22:40
Be bold, choose your own font, don’t let websites dictate the font.
Comment by Didier Stevens — Monday 29 October 2007 @ 22:55
Two years ago I wrote some tests to check this “live” with your security software. It consists of (harmless) demos trying to exploit old security holes in IE — an original and obfuscated versions with NULL bytes. You can still find them on:
http://www.heise-security.co.uk/services/browsercheck/demos/ie/null/
bye, ju
Comment by Juergen Schmidt — Monday 29 October 2007 @ 23:12
Panda version 9? Isn’t that like, a 3 year old version of the software? Good grief!
Comment by bilzner — Monday 29 October 2007 @ 23:17
[…] Didier Stevens recently took a closer look at some Internet Explorer malware that he had found, something surprised him […]
Pingback by [Explorer malware that]-When antivirus products (and Internet Explorer) fail you « Malnews3’s Weblog — Tuesday 30 October 2007 @ 7:15
[…] Didier Stevens recently took a closer look at some Internet Explorer malware that he had found, something surprised him […]
Pingback by ippimail.com » Blog Archive » When antivirus products (and Internet Explorer) fail you — Tuesday 30 October 2007 @ 7:56
This really illustrates my fundamental problem with Microsoft’s attitude.
“The data you have is not accurate. Here, let me fix it for you.”
As if Microsoft is the sole determiner of what constitutes accurate data and what doesn’t.
At work, we work with CSV files a lot. I had to threaten one technician with getting fired if he continued to look at CSVs in Excel to determine problems with them. Microsoft would of course strip out whatever it didn’t like, which made diagnosis nigh-on impossible. Opening CSVs in Notepad was better… but ultimately everyone ended up switching to Emacs or PFE.
Comment by barbecuesteve — Tuesday 30 October 2007 @ 13:19
[…] A000n0000 0000O000l00d00 0I000E000 00T0r0000i0000c000khttps://blog.didierstevens.com/2007/10/23/a000n0000-0000o000l00d00-0i000e000-00t0r0000i0000c000k/http://it.slashdot.org/article.pl?sid=07/10/29/1747237 […]
Pingback by An old IE Trick -- Script Obfuscation with null bytes between characters - Harry Waldron - Microsoft MVP Blog — Tuesday 30 October 2007 @ 21:12
[…] A000n0000 0000O000l00d00 0I000E000 00T0r0000i0000c000khttps://blog.didierstevens.com/2007/10/23/a000n0000-0000o000l00d00-0i000e000-00t0r0000i0000c000k/http://it.slashdot.org/article.pl?sid=07/10/29/1747237 […]
Pingback by An old IE Trick -- Script Obfuscation with null bytes between characters - Harry Waldron - My IT Forums Blog — Tuesday 30 October 2007 @ 21:13
In your video demo you demonstrate that the virus scanner fails to detect the harmful file when running an on-demand scan. However, loading the file into Internet Explorer and allowing the Blocked Content causes the real-time scanner to detect the threat. It might be worth adding to the article that, although anti-virus scanners are being tricked, they are still able to mitigate the threat in a realistic situation such as when a potential victim visits an infected page.
Regards, Simon.
Comment by Simon Edwards — Wednesday 31 October 2007 @ 10:43
I’ve just read hte article and (with growing amazement) the reactions. The reactions show me a few things:
– People (users/administrators) seem more interested in finding reasons and/or excuses to stick with the av software they currently use. And in the process display a ‘hope’ that eg recent updates will have improved the result.
– Producers of av-software are more interested in showing the proper procedure to follow when dealing with this sort of malware in order for their product to produce a positive result. Which to me does not prove the software will function as required all the time. To me this is like creating a false sense of security, where i personaaly think it would be better to advise everyone NOT to rely on any single product if and when security matters.
– Finally it really is amazing that noone suggests that it may be a good idea to make sure that browser software (ie or any other) behaves in this way. With respect to the av software: what is the reason for ignoring (being fooled by) ANY number of nulls??
With kind regards, Peter
Comment by Peter Bosveld — Wednesday 31 October 2007 @ 12:25
[…] Scanning Scripts Filed under: Quickpost — Didier Stevens @ 10:32 After reading my zero byte padding post, someone asked me how McAfee intercepted […]
Pingback by Quickpost: Scanning Scripts « Didier Stevens — Saturday 3 November 2007 @ 10:34
Actually, considering Microsoft will change their implementation without any notice, it makes far more sense for any AV provider to intercept code just before it is executed by IE and check for malware than it does for them to cover every quirk of IE browsers.
From a security point of view, the exploit is in IE. Provided my AV finds the trojan in it’s native form and the webscanner it has can detect it before it is executed, I am happy.
Comment by Miles — Friday 18 January 2008 @ 10:02
[…] Didier Stevens recently took a closer look at some Internet Explorer malware that he had found, something surprised him somwehat. He discovered that the IE-targeted malware had been obfuscated […]
Pingback by storywriter » Blog Archive » When AntiVirus Products (and Internet Explorer) Fail you — Saturday 6 September 2008 @ 20:22
[…] Filed under: Malware, Quickpost — Didier Stevens @ 22:30 One year ago I blogged about an old IE trick still being used by malware. What can be said now that I resubmitted my test files to Virustotal […]
Pingback by Quickpost: “An Old IE Trick” Revisited « Didier Stevens — Saturday 1 November 2008 @ 22:31
[…] Stevens recently took a closer look at some Internet Explorer malware that he had uncovered and found that most antivirus products that it was tested against failed to identify the malware […]
Pingback by AntiVirus Products Fail to Find Simple IE Malware | External Brain — Monday 20 September 2010 @ 0:29